Dear Amped blog fellows, welcome to a brand new Tip Tuesday! When you need to check the integrity of an image, nothing is better than having a reference picture to compare with. Unfortunately, it is common not to have it! That’s why Amped Authenticate lets you search for images from the same device model on the web. Keep reading to find out how!
If you’re a loyal follower of this blog, then you surely know that digital images carry a lot of information besides pixels. There are metadata, and there is information relative to how the image is stored to file: format, file structure, JPEG Quantization Tables, etc. This kind of information turns extremely useful when your task is to check image integrity. Indeed, if someone claims that an image is an unaltered, camera original file, then we expect its features to be totally compatible with other pictures produced by the declared device model.
Let’s work with an example: as part of an investigation following a car incident, we are asked to assess whether this image below is a camera original file produced by a smartphone, model Sony D5503, commonly known as Xperia Z1 Compact (click here to download the full-resolution file).

We fire up Amped Authenticate and begin with filters in the Overview category: the Visual Inspection filter does not raise any concern. We then turn to the File Format filter, which produces this output:
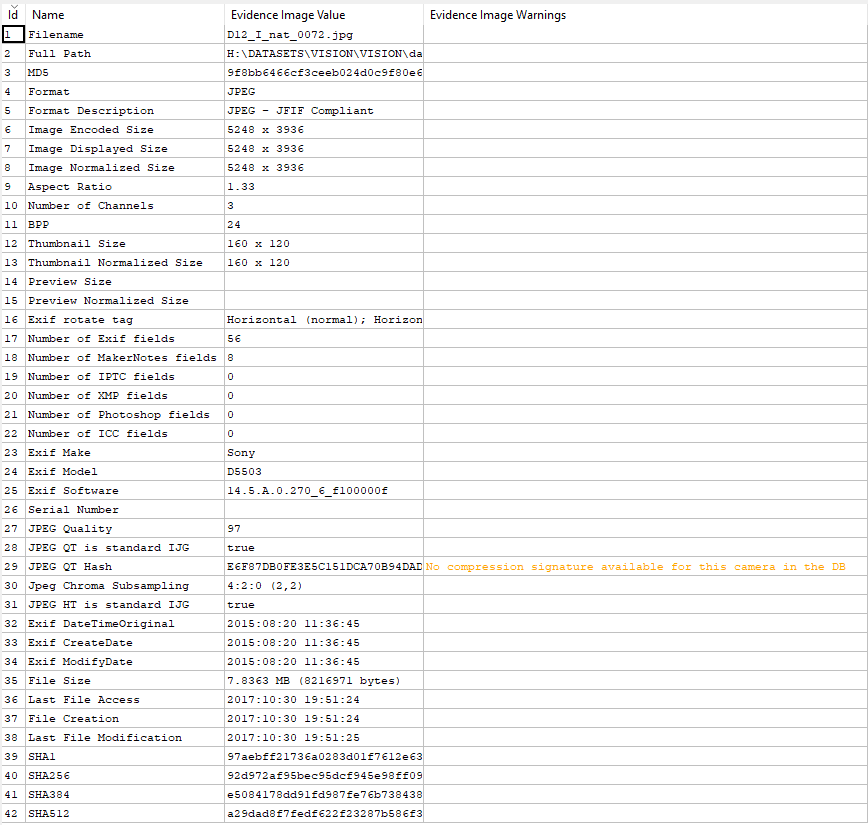
We are happy to see there are no hard warnings (that would be written in red in the right column), but we have a soft warning (written in yellow): it says Authenticate’s JPEG Quantization Table database does not contain any compression signature for this camera. Alas, we miss that one! Does that mean that the image has an issue? No! It means Authenticate cannot confirm that its QTs are the expected ones, simply because this device model is not in Authenticate’s internal DB.
Are we left alone? Of course, not. Amped Authenticate has a tool that allows you to search for images of a given make and model on the web. Just click on Tools -> Search Images From Same Camera Model… and you’ll get this dialog:
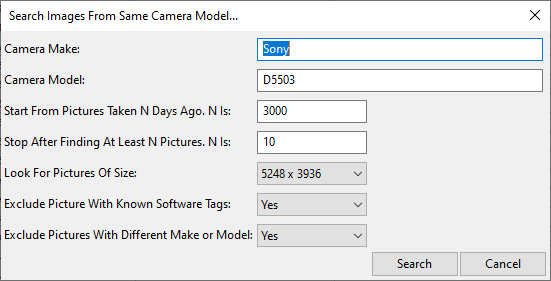
Authenticate will look for images that declare in their metadata to come from a Sony D5503. Not only: it will exclude by default all images whose Exif “Software” tag contains any known software name (because we want good reference files, not modified ones!). In our case, forcing the same resolution of our evidence file would return only two files, so we opt for allowing images of any size, thus obtaining this table:
The table lists images that are freely available on Flickr and tells you their URL, the date they were uploaded, the ID of the user that uploaded them, and more info.
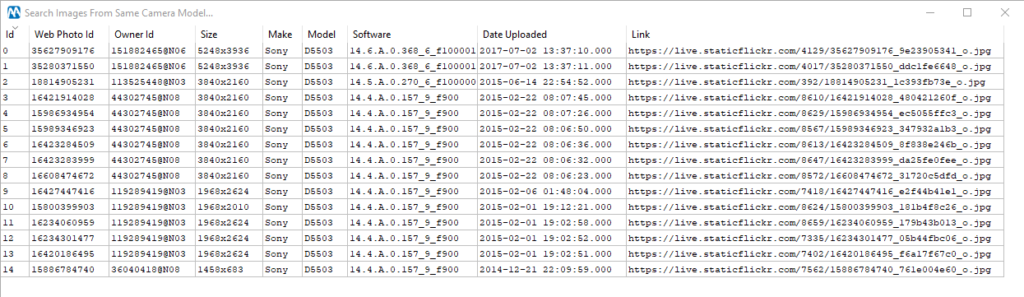
We can select them all, right-click and Download Images, then choose a destination folder. Once they’re on our computer, we can run the Batch File Format Comparison tool, from the Tools menu. This is what we get (we’ve hidden some column of the table for better visibility):
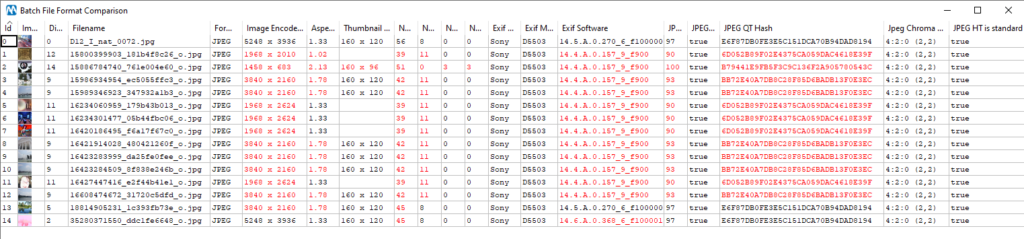
Our evidence image details are written in the first row of the table, then other images are listed. For each reference image, values that are different from those in the evidence are highlighted in red. Notice that, while most images have different JPEG QT, there are two at the bottom of the list that match exactly. Interestingly, the penultimate is also the only one that has the same firmware as our evidence image (according to the Exif Software field).
It is worth the effort loading this image as reference for a deeper comparison: just right-click on that row and select Load as Reference. We can now compare the two images’ characteristics in detail: let’s begin from the File Format filter:
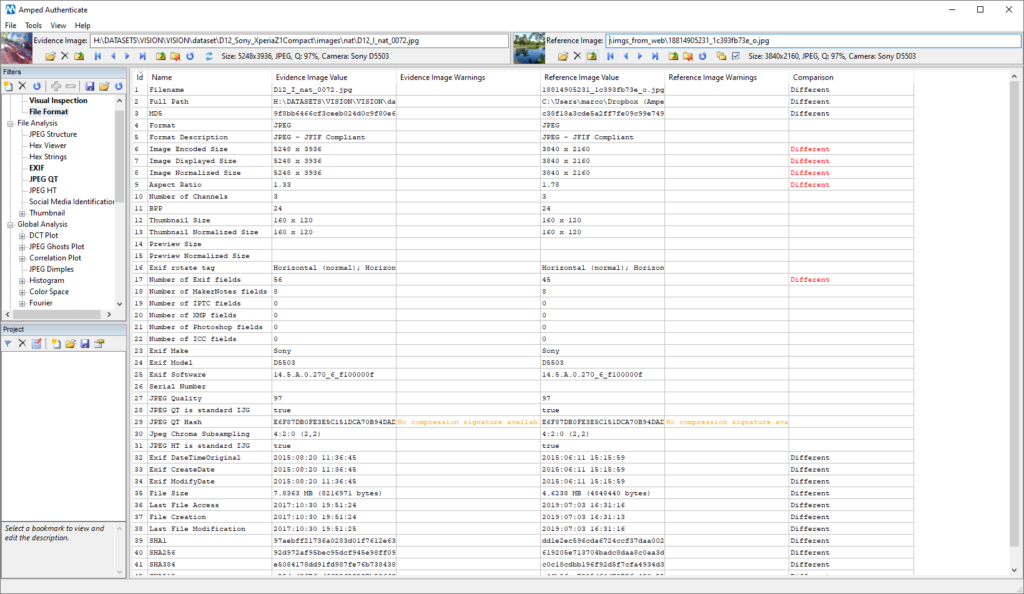
As expected, the reference image has a lower resolution. Is it a supported resolution for this device? A quick search reveals that yes, it is (see here). So that does not invalidate our comparison. We then see we have a different amount of Exif metadata. Let’s check what the Exif filter has to say:
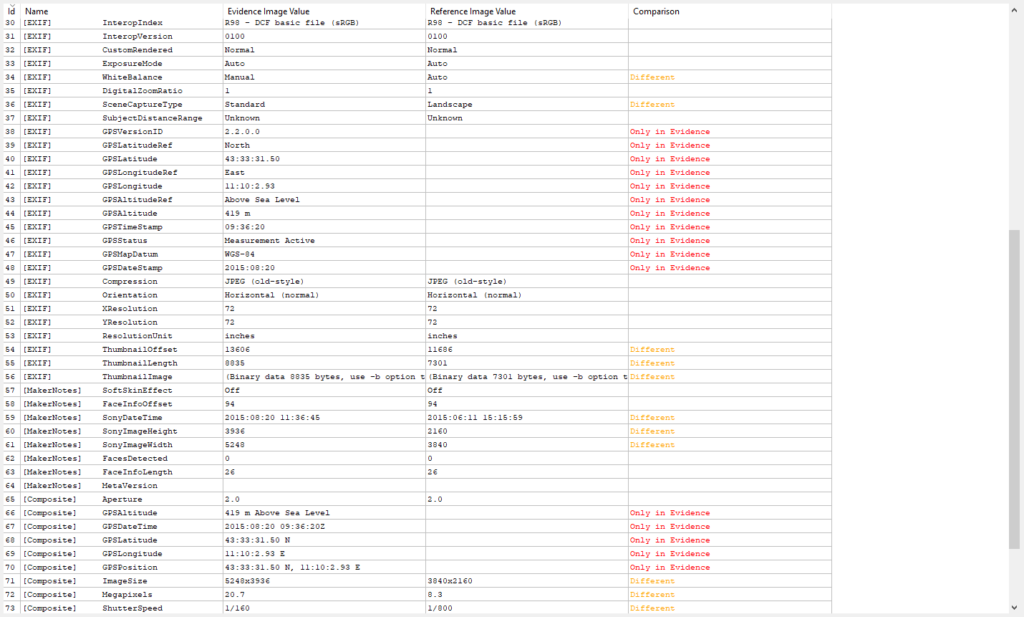
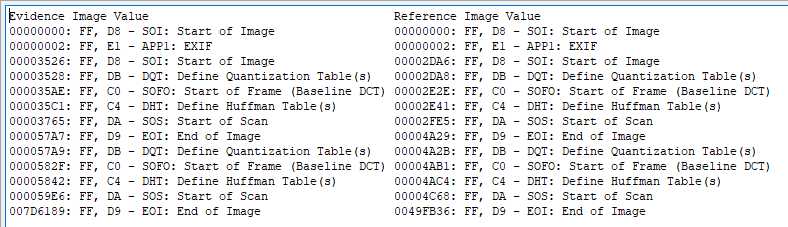
Good! The different amount of metadata is simply due to the fact that the GPS localization feature was probably turned off in the device that captured our reference image. This is a user-configurable option, so we must allow for differences between the evidence and reference file. We can then compare the JPEG Structure filter output, to see whether files are the same even from the structural point of view. This time, we have total compatibility (we don’t expect the offset values, that are the 8-digit numbers written on the left, to be the same; we only expect lines to be in the same number and order).
We managed to find an image on the web that is strongly compatible with our evidence image. Of course, that does not provide rock-solid proof about our evidence image integrity, but we are certainly more inclined towards considering it a camera original file than before.
Before concluding, let us just mention that Amped Authenticate features another, even more powerful, tool to search the web for reference material: it is called Search Images from Same Camera Model (CameraForensics)… , under the Tools menu. We’ll dedicate a future Tip to this tool and to show the difference from the one we’ve used today.
This week’s takeaway is: comparison with reference material is the best way to go for integrity verification! If you don’t have reference images from the same device, you can use Authenticate to search the web for them.




