Welcome to this week’s Tip Tuesday! Today we are showing you an interesting, perhaps a bit hidden, functionality of Amped Authenticate. There is no need to introduce the PDF file format: it is surely the most widespread format for sharing digital documents. Therefore, it may easily happen that you have to deal with a PDF containing images and that some of them get questioned.
What would you do in such a case (after realizing that if you drag-and-drop the PDF into Amped Authenticate, nothing happens, because it’s not an image file)? Would you take a screen capture of the picture and work with that? “Nooo!” – I hope you said! Screenshots are evil for image forensics! Ok, you would get some pixels to work with, but you would lose all metadata, you would lose encoding properties, you could be recompressing data… That means you cannot check image integrity, and finding manipulations becomes much harder. No, there’s a better way of dealing with images embedded in PDFs, and we’ll show you how!
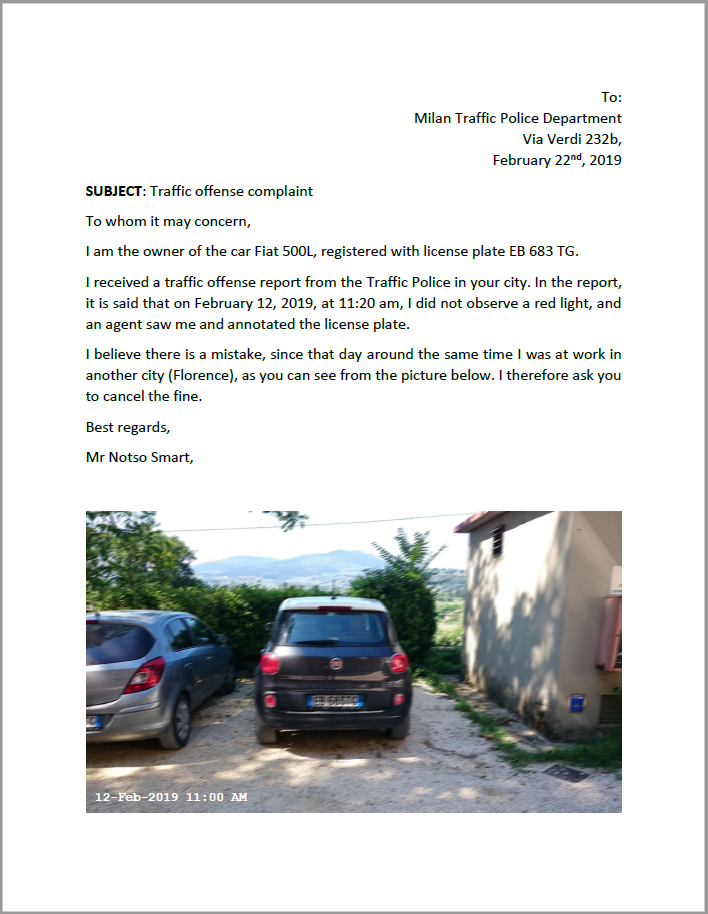
Let’s imagine you work for a Traffic Police Department, and you receive this PDF document from a driver who was fined (click on the link below to download the PDF)
The tool you need is just under the Tools menu in Amped Authenticate:
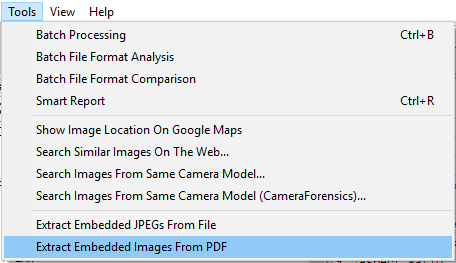
Just click on Extract Embedded Images From PDF and select the PDF file using the file browser that pops up. You will then be prompted about some options:
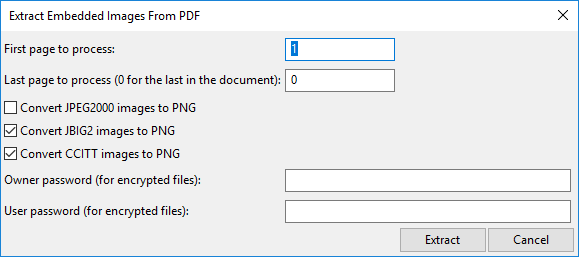
In our case, the PDF is not password protected, and we have only one page, so we’ll just leave the default settings and click on the Extract button. Images will be immediately extracted in a folder located next to your evidence image.
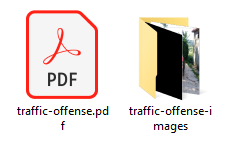
Just open the folder and load the image showing the car into Amped Authenticate.
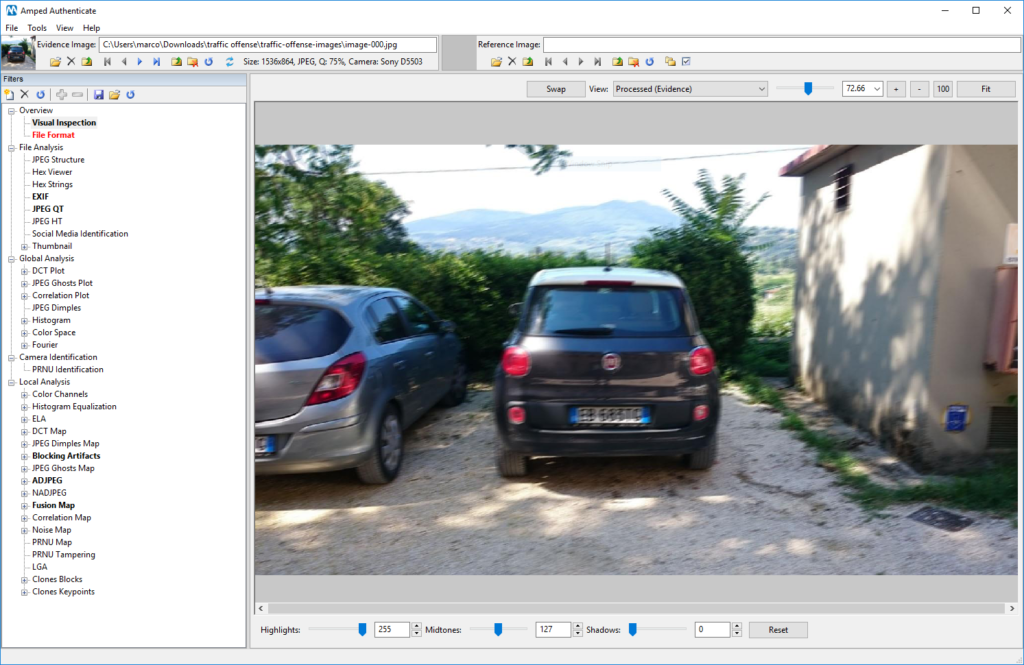
We immediately notice that the date and time overlay (that you could see at the bottom-left in the PDF image) is not really part of the image. It was likely overlaid with a document editor, and it is stored as a different object in the PDF file. Let’s now take a look at the image using the File Format filter:
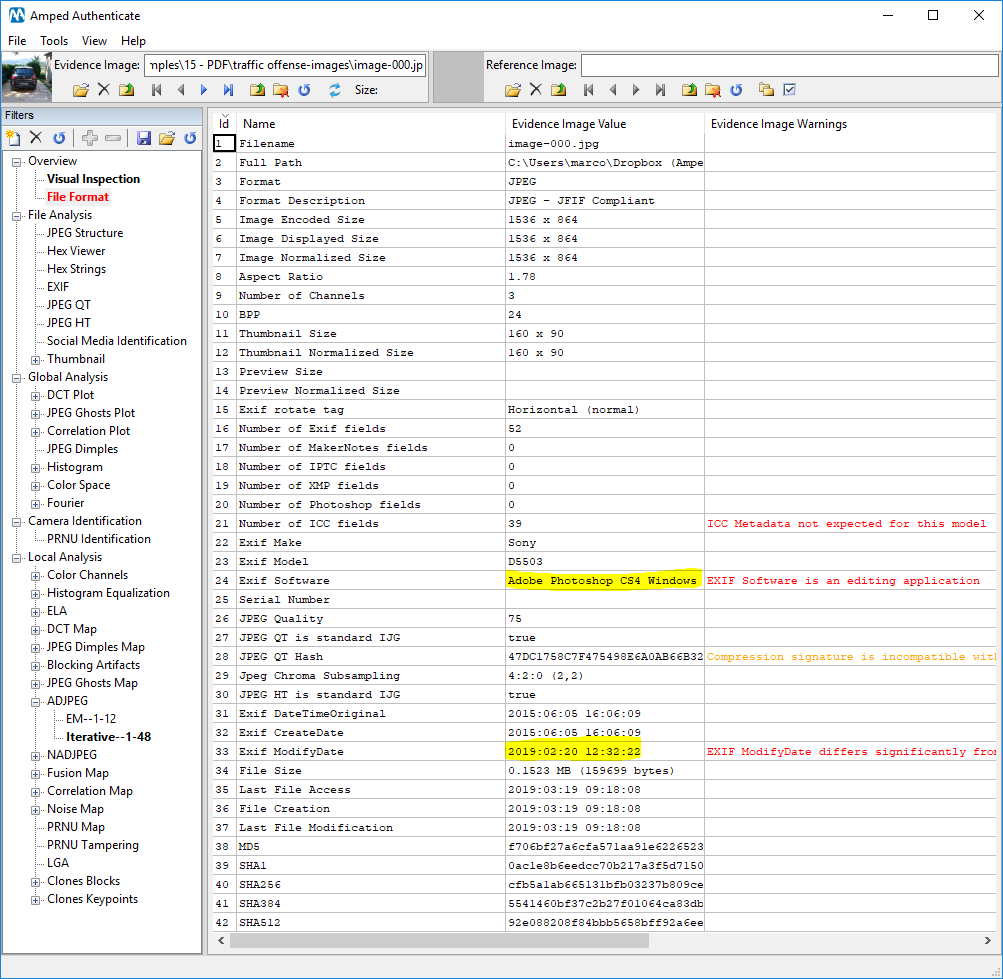
There are traces of processing with Adobe Photoshop left in the Exif metadata! Not only, Exif dates tell us that the image was captured well before February 2019, but it was edited on February 20th, 2019!
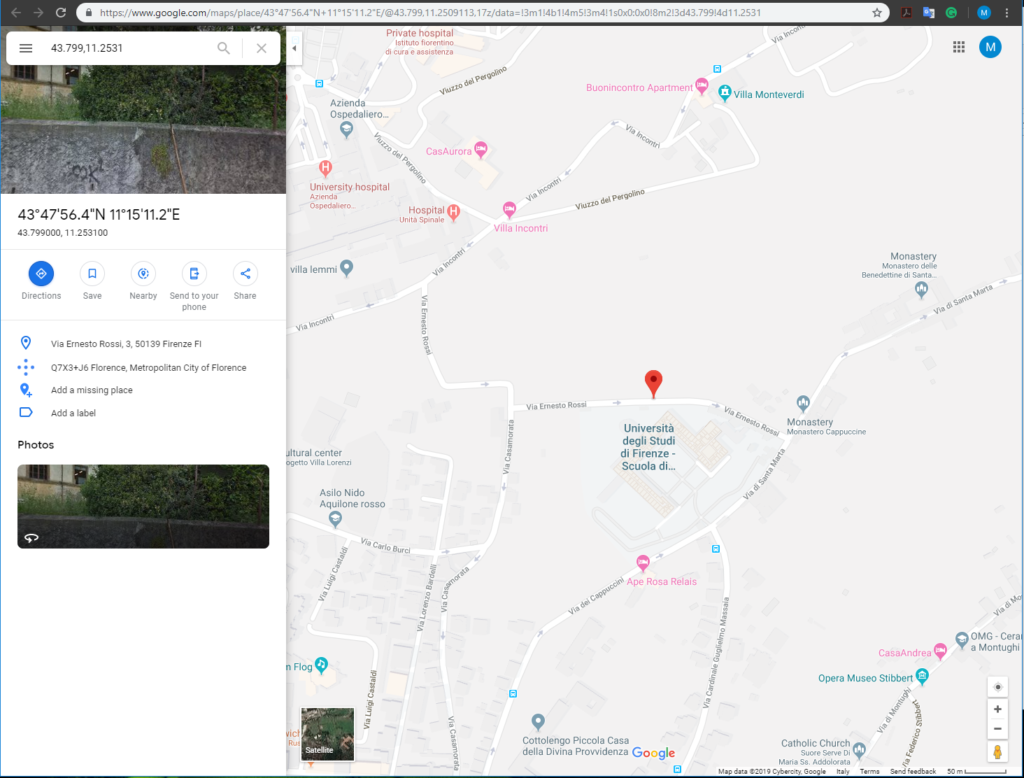
We notice there is plenty of Exif metadata: taking a look at them with the EXIF tool reveals that the image also contains GPS coordinates, that can be readily turned to a place in the world, using the Show image location on Google Maps tool (under the Tool menu). Isn’t it great that you can still find GPS information in an image stored inside a PDF?
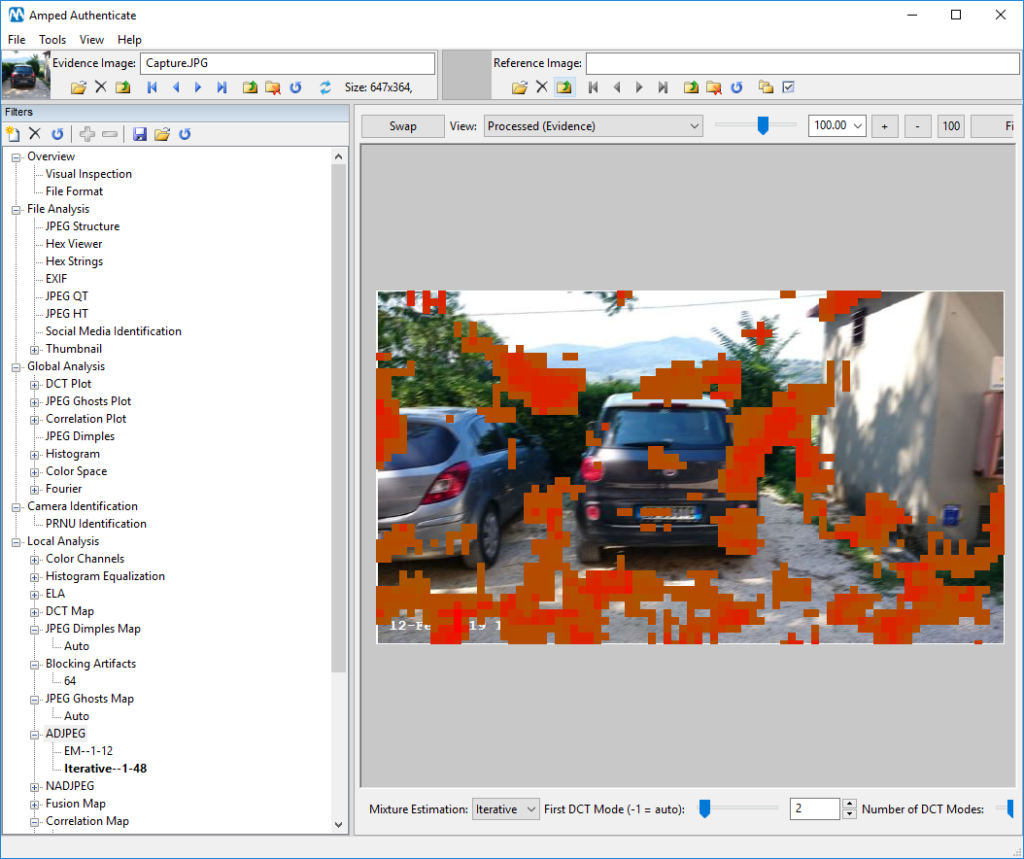
While all these inconsistencies with Exif dates and software could be enough to discard the document’s reliability, we cannot resist taking a tour in the Local Analysis. Among the others, the
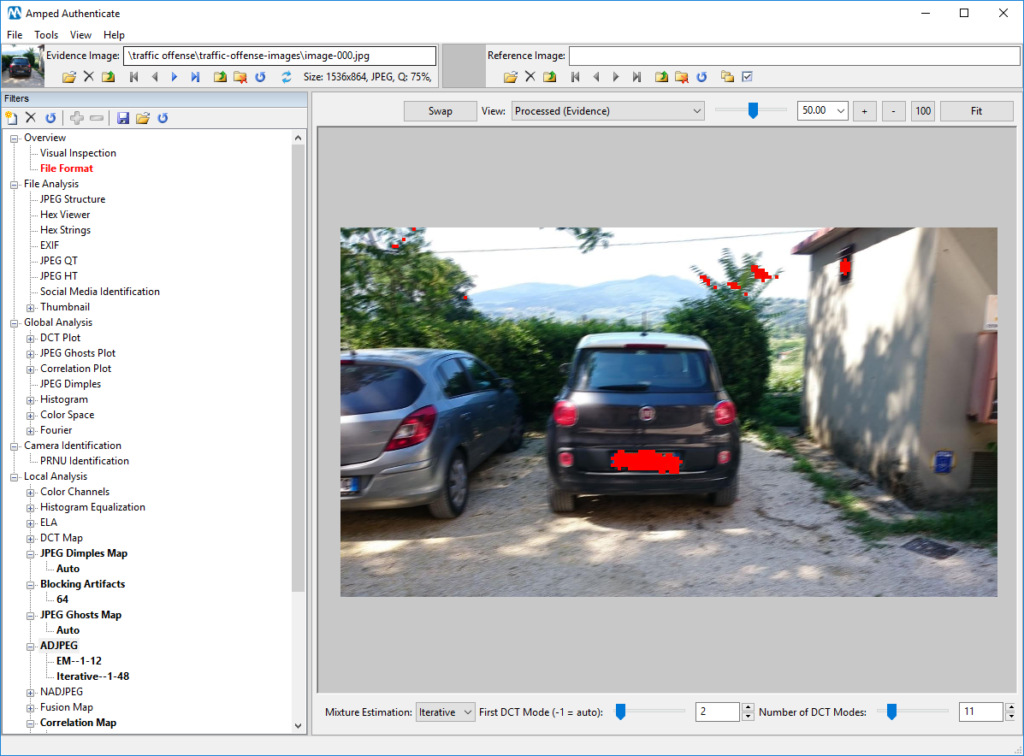
Not only was the picture likely taken at a different time than the one declared in the document: the license plate was also likely tampered with!
To further stress the importance of having used the Extract Embedded Images From PDF tool, let us check what would have happened if we had taken a screenshot of the image and saved it to a JPEG file. The very same
There’s no need to comment: we’ve lost everything! And, of course, metadata are also gone (because when you screenshot you are creating a brand new file).
Time for this week’s takeaway: always use the right tool for the right job! When you’re dealing with a PDF containing questioned images, extract them as Amped Authenticate allows you to do.




