As Amped Authenticate users hopefully learned during our training courses, authenticating a digital image means much more than attaching a fake/real label to it. In some cases, you may be asked whether the integrity of a questioned digital image is preserved (or broken). In such a case, forgery localization tools should not be your first choice from Authenticate’s powerful arsenal.
Indeed, proving that the integrity of an image is “broken” means demonstrating that the image file is not the original file produced by the acquisition device; instead, it has been processed after acquisition. “What” happened during the processing may even not be of interest, because in some cases broken integrity alone is enough to discard a potential evidence.
That’s why we always stress the importance of tools under Amped Authenticate’s File Analysis category: they are the best way to screen image properties, metadata and coding details looking for unexpected or suspicous elements.
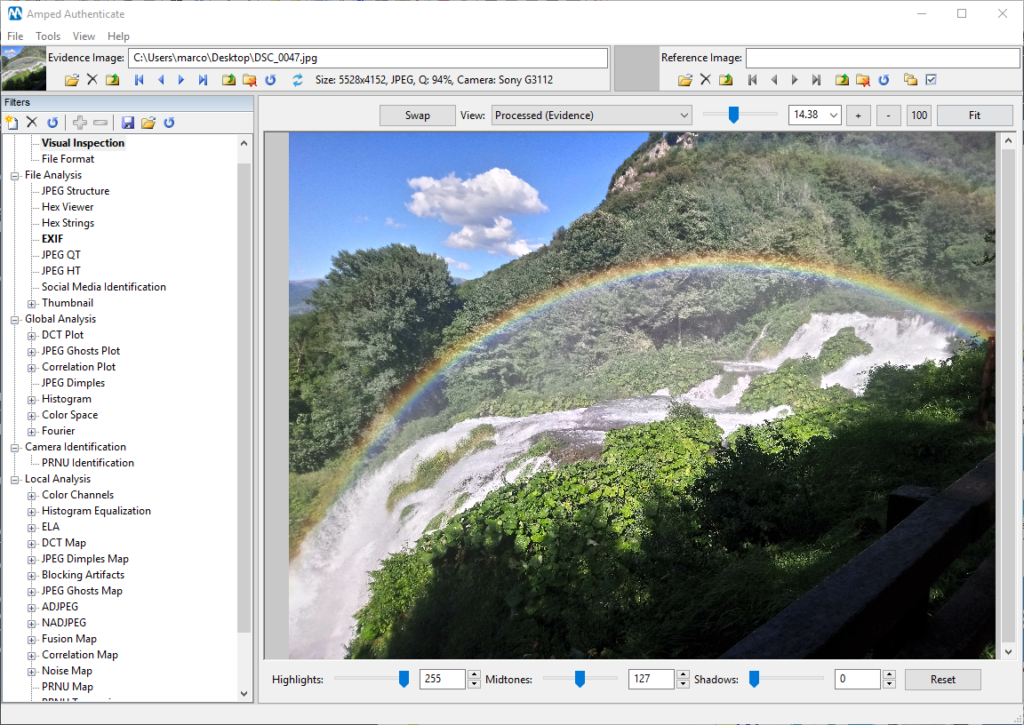
In this post, I’ll share with you a tip that could prove important in your cases: check for un-updated Exif image resolution tags! Let’s take this nice picture from a Sony Xperia XA1 smartphone (formally called G3112), and let’s imagine we are asked to validate its integrity: is this an original file, untouched since acquisition?
To start, there are two things we can do:
1) Since the supposed originating device is known, we can search for reference images captured with the same camera model (possibly running the same firmware). We will then compare these reference files with our questioned image.
2) Search for anomalies in image format and metadata.
Point 1) will be the object of a coming-soon Tip Tuesday, so we will not dig into it now. For the sake of this Tip, it’s enough to know that even if we run the “Search images from same camera model” tool with default settings, we find no images. That’s a bit alarming, but still inconclusive.
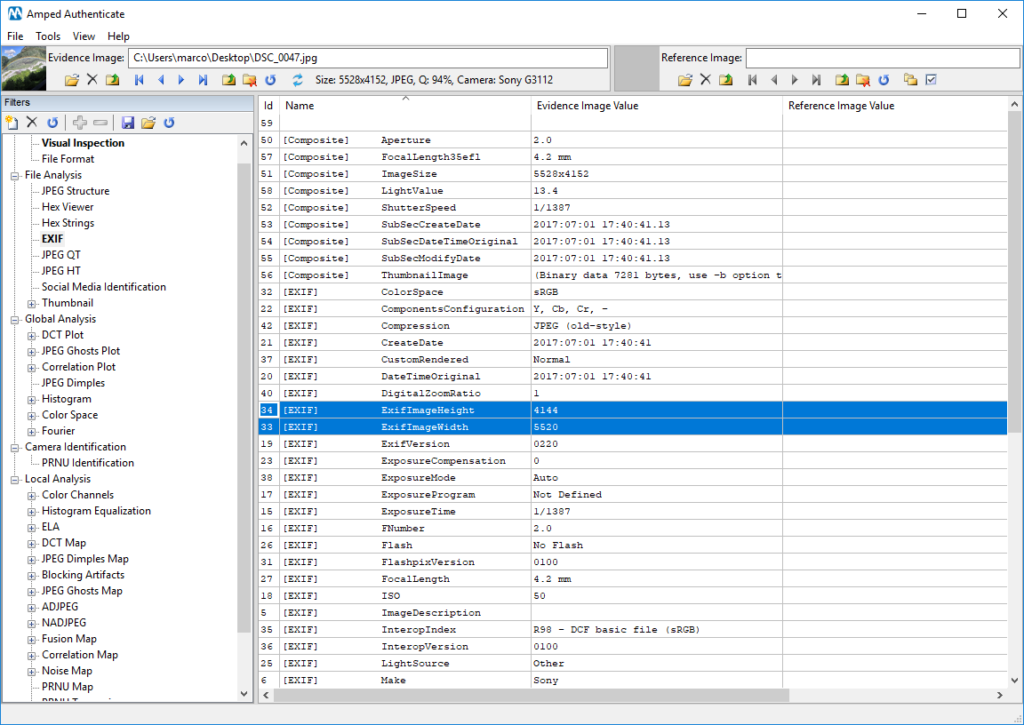
Let’s move to point 2), then, and take a look to Exif metadata. At a first glance, everything seems just fine: no traces of editing software, “Make”, “Model”, and “Software” Exif metadata are just as expected; Create/Modify dates match to the second, and we also have a lot of typical acquisition-device written tags, like ExposureTime, FocalLenght, etc.
Everything fine, then?
Well… not really! If we look closer, we’ll notice there are two tags called ExifImageWidth (valued 5520) and ExifImageHeight (valued 4144). Unfortunately, the actual image resolution is 5528×4152!
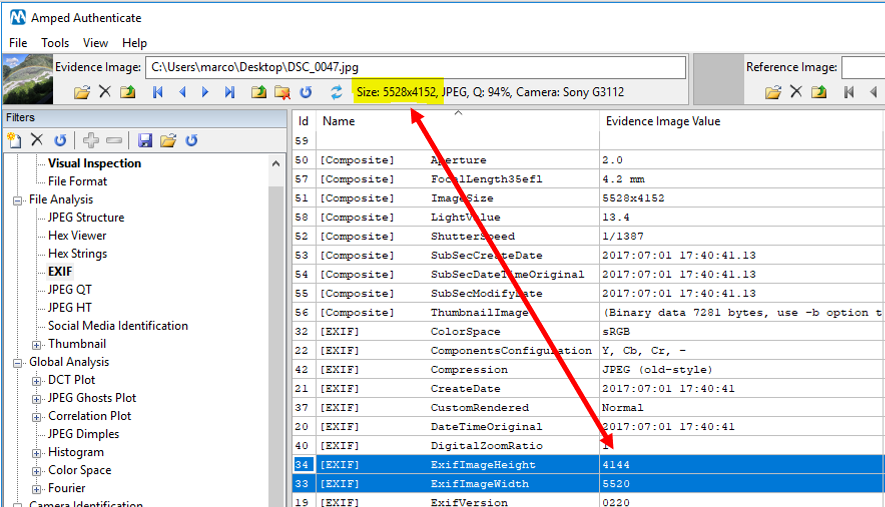
To me, that is enough to seriously question image integrity. When you have tags whose values are not consistent with the actual image properties, it is very likely that a software was used to manipulate the image, and that the software simply forgot to update some Exif tags (or, even worse, put duplicated tags with new values without removing the existing ones).
If we look in the datasheet of the camera model, we’ll see that 5520×4144 is the resolution actually supported by an Xperia XA1. This
Now, you may be wondering: “Okay, but are situations like this going to happen in practice, or are these “lazy software” very rare to find?” Well, I’m glad to tell that if you own a computer with Windows, you can freely reproduce the situation above using the good old MS Paint: open a JPEG file that has the ExifImageWidth and ExifImageHeight tags, resize it and save it as JPEG: you’ll see that tags won’t be updated! (Tested on Windows 10 Pro – 1803). There are also other examples of the same problem in history: for example, ImageMagick seems to have suffered the same problem ( read more ), preventing some photo libraries to properly open files because of the wrong information left in Metadata.
The take-away of this week is: devil is in the (Exif) details!
I hope you enjoyed this Tuesday’s Tip! Stay tuned and don’t miss the next ones!




