In this post on CCTV Acquisition, we will provide a base for the series by breaking down CCTV into a relatively easy chunk. Understanding CCTV could be a series in itself. Nonetheless, we feel it’s essential to understand how CCTV works before getting into the weeds of recovering it.
CCTV stands for Closed Circuit TeleVision and derives from the time before computer networks or video streaming. The “Closed Circuit” comes from the fact that the video signal could be viewed and recorded. However, there was no method to transmit or share it outside of the cabled infrastructure.
In today’s world, although many are still “closed”, most modern systems have the ability to transmit and share data. Subsequently, you will find that many documents now refer to Video Surveillance Systems (VSS) rather than CCTV.
Within those systems, there can now be several recording components. The moment that an item is installed into a system that is capable of recording and retaining data for further use, it is in effect, saving potential evidence.
All cameras start with a lens and then a sensor to convert what the lens is “seeing” into information. This is where things now get interesting as there are two main camera types: analog and digital.
Analog Camera
For the analog camera, the sensor turns the visual information into an electrical signal. This signal is fed down a cable to a device capable of turning that signal into a visual image, such as a monitor. For those old enough to remember, the recording device usually put in-between the camera and monitor used to be tape. Now it’s a box a bit like a computer, called a Digital Video Recorder (DVR). The DVR converts the analog signal into digital data and that’s where it is retained.
The identification of an analog camera is important during the initial scene assessment as the recorded footage may require specific processing stages. We will look more at this later in the series.
Digital Camera
A digital camera turns the sensor image into digital data directly within the device. The data is then transmitted using transfer protocols to a storage device now known as a Network Video Recorder (NVR). Again, there would usually be a monitor to view and access the stored material. Some digital cameras also have a small storage device housed within the camera itself.
Hybrid Recorders for CCTV Acquisition
Devices that are able to deal with both camera types are known as hybrid recorders.
Regardless of the type of camera, these different recording devices are the crux of this blog series. We will be looking at other types of devices and other system configurations but, for the main part, it is these systems that will take up most of our time.
These are the devices that hold the footage you need to answer questions about within your investigation. This data is the evidence. The picture is formed from this data, not the other way around.
Digital Data
To start with, you have the visual information, the video. Then, you may also have audio. Also, you will have timestamp information that connects the video and audio with the date and time that the data was captured. Moreover, you will have camera information, which may simply be the camera number or name. It may also refer to other information such as recording type.
Storage
Finally, the recorder’s storage system will often contain information surrounding device access, user control, power outage, etc. The amount of extra information is often directly related to the system’s complexity. A small 4-camera system may only store the video, along with the date and time. However, a large 250+ camera system with storage spread over multiple devices may store all access and user-control logs, etc.
To summarize so far, we have a storage device that holds the data we require. Before we dig a little deeper into this data, we must understand that they cannot record everything, forever. They are limited in the amount of data they can retain.
4-camera System
To understand this, let us consider a basic 4-camera analog system with just a date and time index. Inside the device, there is an analog-to-digital conversion chip that can process video at a certain speed. This is usually referenced as Frames Per Second (FPS). In our example, the chip can manage 50 FPS.
If the device is set to record the maximum frames for all cameras, the frame rate for each camera would be 12.5 FPS. If the user has control of the settings, they would be able to set 1 camera perhaps to 25FPS, then one camera at 15, and two cameras at 5.
DVR
Our basic example DVR has three quality settings. This controls the amount of compression that is applied after the analog-to-digital conversion. Having high compression would mean lower quality and vice versa.
Most systems also have a frame size option. This controls how many pixels, the smallest part of a digital image, should be used to make up our encoded video frame. They are often referenced by the width and height, rather than the total pixels. For example, 704 pixels x 576 pixels.
There could be various other settings but we have covered the standard three that control the amount of data that can be fit ono the storage device within the recorder.
Within the storage device, all our data is stored on a Hard Disk Drive (HDD). They are very similar to those found in standard computers but often optimized for 24/7 running. Just like the ones within your computer, they are restricted in the amount of data they can hold. This is known as the system’s retention period.
With full FPS, the highest compression quality, and then then the largest frame size, our system may be able to record 10 days worth of footage before it starts to overwrite the oldest data.
In contrast, with 1 FPS on all cameras, low-quality compression, and then a small frame size, the owner may be able to achieve a 6-week retention period.
Remember
High frame rate, high quality, large frame size = Lower retention but better evidence.
Low frame rate, low quality, small frame size = Higher retention but a reduction in the evidential quality.
To recap, we have a HDD within our recorder and its storage time is limited. If it’s not recovered, our evidence could be overwritten and lost forever.
Now let us look in more detail at the data that may be stored on this HDD. To start with we have operating system data. This relates to what happened within the system.
Did someone access it? Was camera 4 disabled and set to not record? Did someone change the date and time?
Then, we have the important camera data. This consists of the video, audio, date and time, and recording information.
We will look at operating system data further on in the series. Let us concentrate on the camera data for now, as this is what is most often required.
Camera Data
Someone new to this industry may be shocked to learn that although a surveillance system storage device is there to retain data, there are no standards on how that data is actually retained. We have ended up in a situation where a company can record an event but not actually have to disclose how it was recorded. They can even record something in one way and then play it in a different way.
The lack of standards within the recording data is the reason why evidential integrity must be preserved. You must always be able to start from the beginning, whatever that may be. Remember that this data will be overwritten very soon so you cannot simply go back and get it if required.
What if we had an NVR with 16 channels? This means it can input 16 cameras. It can also take in 4 audio sources. Some cameras now have small microphones on them, or separate microphones can be attached. The system would also have date and time information that connects the recorded material to the date and time set within the device.
Internal HDD
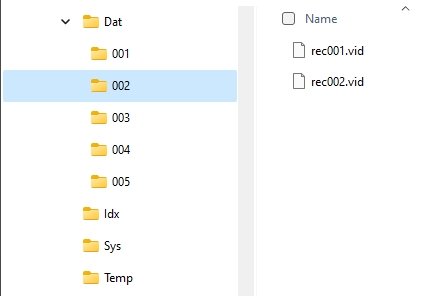
If we look at how the data is stored on the internal HDD, in general, it is often either file-based or data-based.
If you were to plug the HDD of a file-based system into a computer, it would likely be able to read the folder and file structure. We would be able to see “Files”.
However, for a data-based format, the drive is simply one huge storage bin. The data is controlled by the indexing system within the recording device. It is for this reason that computer examiners often plug in a CCTV HDD and cannot read any of the data, even when using computer forensic software. Dedicated CCTV HDD software would be required in this instance as the data is not arranged according to a known file system.
Both methods have video, audio, and the date and time. This is where things can get a little confusing as, remember, surveillance system manufacturers have free reign to do what they want. They may start with a known standard for recording but then modify it.
Video and Audio Codec
In our example system, they have not modified the video. They have retained an encoding standard called H264. This is known as a CODEC, which stands for Coder and Decoder, or Compressor and Decompressor, depending on what you are reading. We will look more at codecs further along in this series.
For the audio, they have modified an older telephony codec. For the date and time, they have developed a proprietary storage method to store this data and link it to the video and audio.
The consequence of the three different components being constructed differently is that although the video can be decoded independently, the audio, the date and time may require some work or the use of dedicated forensic video software, such as Amped FIVE.
List of Acronyms
The following is a list of acronyms that will help you along the way while you read through all our blog series about CCTV Acquisition.
| Acronym | Expansion |
| CCTV | Closed-Circuit TeleVision |
| Codec | enCOder / DECoder or COmpressor / DECompressor |
| CSI | Crime Scene Investigator |
| DEMS | Digital Evidence Management System |
| DME | Digital Multimedia Evidence |
| DVR | Digital Video Recorder |
| FPS | Frames Per Second |
| HDD | Hard Disk Drive |
| NVR | Network Video Recorder |
| USB | Universal Serial Bus |
| VHS | Video Home System |
| VSS | Video Surveillance System |
| WMV | Windows Media Video |
Conclusion
For now, though, we have a basic understanding of CCTV systems and an appreciation of some of the complexities in how they retain data. You should now recognize the importance of recovering the original native data quickly due to limited retention time.
Furthermore, we will build more on the information learned here when we start to navigate a VSS interface and attempt to extract some data from it. However, in the next post, we have ‘Search & Trawl’.
This is one of the most important initial stages before the acquisition, as in order to retrieve it, you must know of its existence.
Until next time, stay safe.