Dear Tip Tuesday addict, welcome to this week’s dose! Today we’re dealing with one of the latest features introduced in Amped Authenticate, the Shadows filter. We’ll see how the filter can help you identify the manipulated object, which is very handy when you’ve selected many shadows in the image. Keep reading!
If you’ve never tried Amped Authenticate’s Shadows filter, you’re definitely missing something! You’ll find it in the Geometrical Analysis category since it aims at detecting physical inconsistencies rather than anomalies at the pixel or statistical level.
The idea is quite simple, the user clicks over a point on a shadow. Then clicks on two more points in the image, which conservatively include the point which is casting that shadow, as shown below:
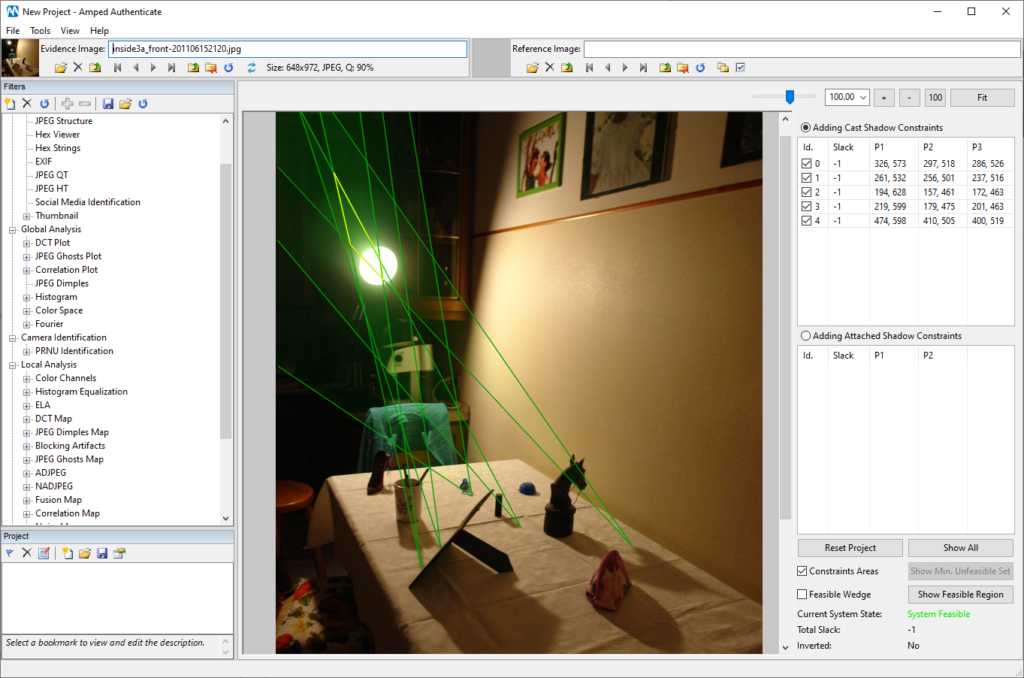
Under the assumption that there’s a single, point-wise light source (e.g. the sun, or a single light bulb or spotlight), the shadow projected by all objects can be used to constrain the position of the light source. Each time a selection is done, a wedge is defined which constrains the position of the light source on the image plane (of course, such position is not necessarily contained within the image). If all the available wedges share a common area (called “intersection”), then shadows are consistent. This is well explained in the image below, where the five green wedges intersect to form the yellow region, which actually contains the lamp.
Now, what happens if the image contains a spliced object? If the object’s shadow has not been forged correctly, when we add the corresponding wedge the system may become unfeasible. It means that there exists no intersection for all the wedges. This is actually what happens in the example below (taken from the great Realistic Tampering Dataset by P. Korus): notice that the system is now marked as unfeasible.
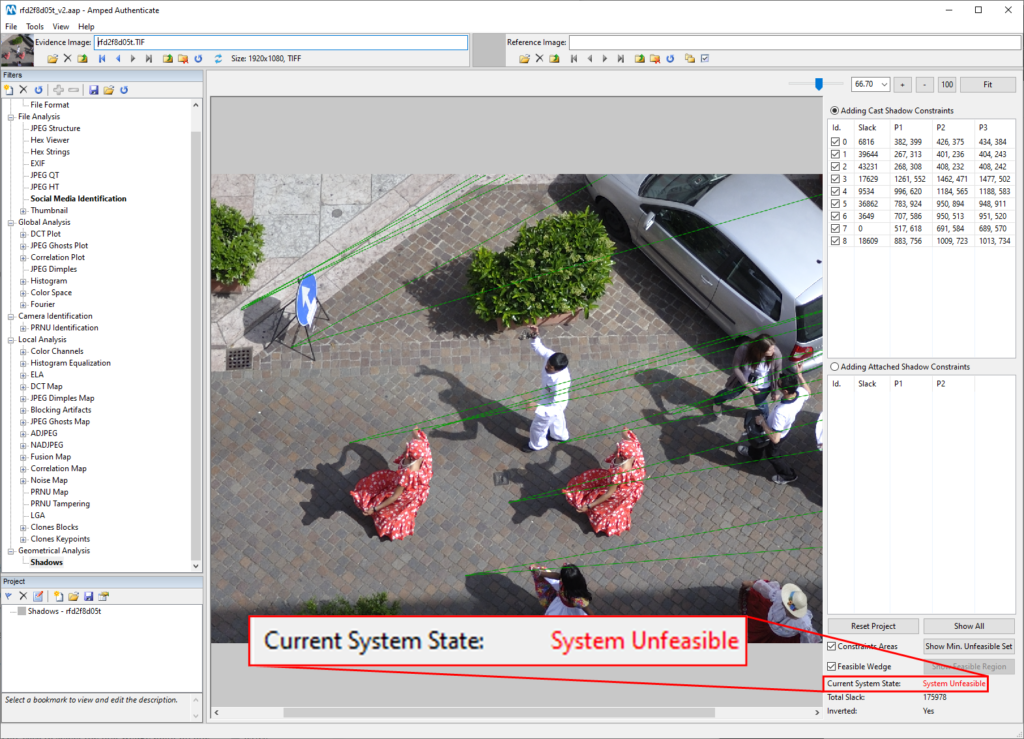
Okay, so we know the above image is fake. But how do we identify the forged object? One possibility is to iteratively mark each constraint as “Inconsistent”, so that it gets excluded from the computation. To do so, simply right-click on it in the list and select Mark as inconsistent. The constraint will become red and it will be excluded from the intersection. If we guessed the right object, then the system becomes Feasible and we’re done. In the video below, we get the right constraint at the second attempt!
However, when you have many constraints, it may take a while to check all of them! And here comes the tip of the day! When the system is in an unfeasible state, a promising Show Min. Unfeasible Set button becomes available:
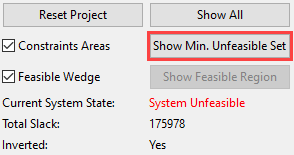
By clicking on it, we’ll let Amped Authenticate automatically combine many possible subsets of constraints, looking for a smaller set of constraints which is enough to make the system unfeasible. This will restrict a lot our search for a fake object! Let’s see it in action:
As you can see, after clicking on the Show Min. Unfeasible Set button, only four constraints remain selected, including the one corresponding to the fake object. We can thus restrict our search to only those.
Notice that, if you go back to the complete set of constraints (by clicking on the Show All button) and then click again on Show Min. Unfeasible Set, you may obtain a different selection! Indeed, there is not a single minimum set of unfeasible constraints, and Authenticate will randomize the search to give you more chances of finding a small subset. Wait, don’t go away! We know the word “randomize” is not very welcomed in the forensic field! Let us defend our choice with two arguments:
- This function does not influence the final decision: it only provides a faster way to reach it.
- Although randomized, the behavior will be the same if you restart Amped Authenticate and work with the filter in the same way. So you can reproduce the full workflow, including the automatic minimum unfeasible set selection provided by the software.
That’s it for today! If you want to download the image we’ve worked on, it’s freely available (as part of a ZIP file) from the webpage presenting the dataset: http://pkorus.pl/downloads/dataset-realistic-tampering




