Hello Amped blog readers! Following last week’s Tip Tuesday idea that “simple things matter”, today we’ll show you how one of the most straightforward filters in Amped Authenticate, that is, the Thumbnail filter, can sometimes reveal interesting information.
First of all, what is the image thumbnail? It is (well… it should be) a much lower resolution version of the image, commonly in the order of 160 x 120 pixels. It is mostly used by file/image manager applications for efficiently creating image galleries: they just need to decode a few thousand instead of millions of pixels during gallery creation and browsing, while the full-size picture will be decoded when the user “opens” it. The Exif standard provides rules for embedding the thumbnail into the image file as a stand-alone JPEG object, allowing to decode it without having to process the full-sized image.
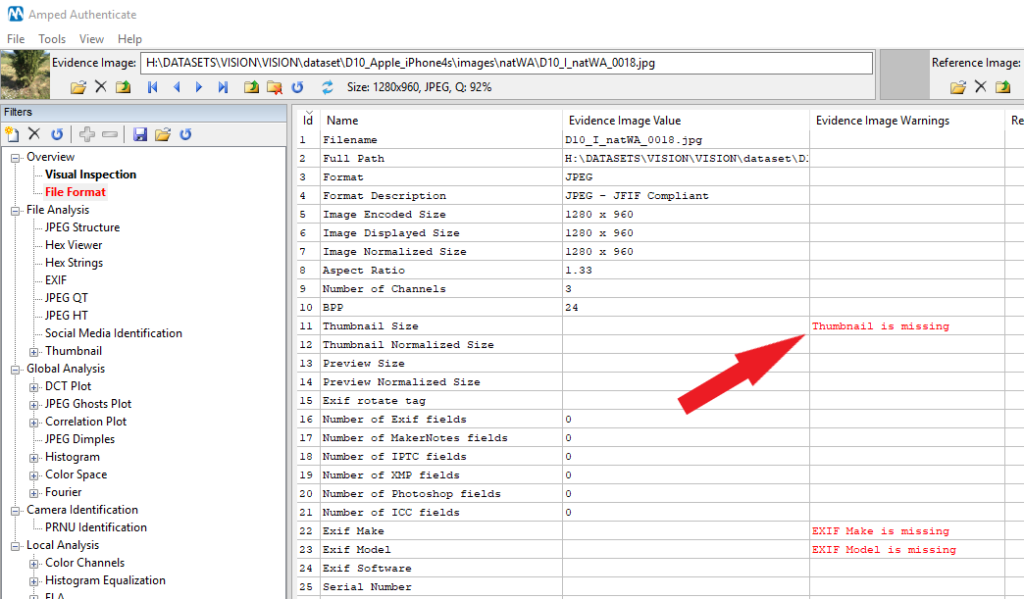
Is it common to find the thumbnail? Definitely YES: the vast majority of modern cameras/smartphones do embed a thumbnail into the image during acquisition (the device itself will be the first user of it when showing the image gallery). Is it mandatory? No, you can strip it out and the image will survive; indeed, most social media do so to save some storage. That is why the absence of the thumbnail is considered a suspicious element during image integrity verification and is signaled by Amped Authenticate’s File Format with a red warning, as shown below for an image sent via Whatsapp.
Some devices also embed an image Preview, that is, a not-so-small image (e.g., a common resolution could be 640 x 480 pixels) that is meant for fast image browsing. Once more, it is an optional element and is less diffused compared to the thumbnail.
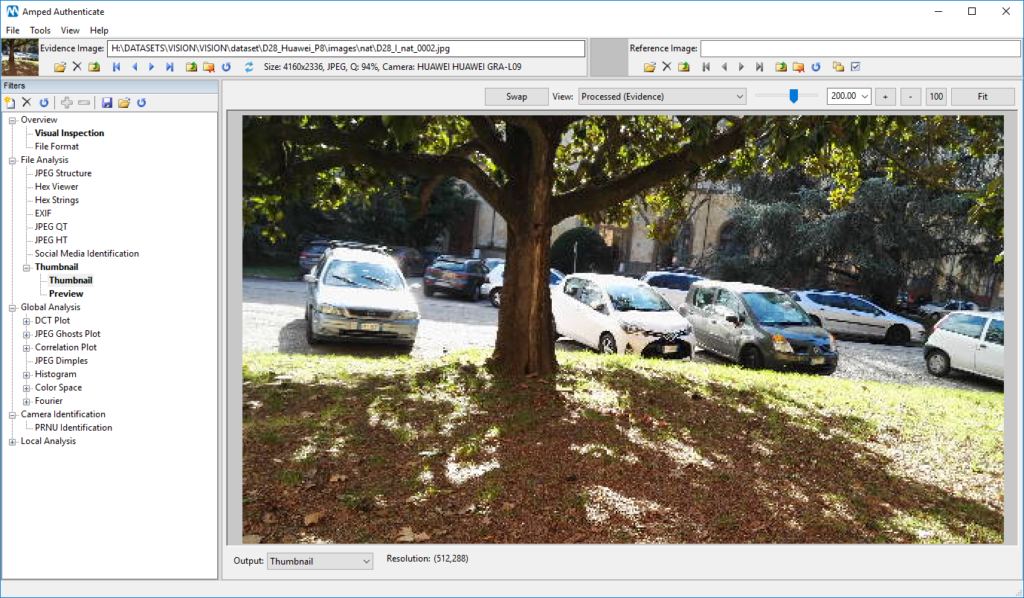
Amped Authenticate’s Thumbnail filter, under the File Analysis category, allows you to see (if they are present) the thumbnail and the preview contained in your investigated image.
Typically, you will find a “very pixellated” version of the full-size image. But, you know, in forensics surprises are always around the corner (and we like this)! It could happen, indeed, that the thumbnail contains more visual content than the main image. There are famous examples of this unusual situation. As narrated in this blog post, in 2006 a celebrity captured images of herself naked, then cropped the sensitive parts using Photoshop and uploaded the picture on the web. Unfortunately, Photoshop had a bug and failed to update the thumbnail! Therefore, people could see the sensitive parts (luckily, at shallow resolution).
“Come on, 2006… those days are gone!”, I can hear you say. Sure, Adobe has fixed that bug, but I’ve recently discovered a very similar issue on my own Sony Xperia XA1 smartphone (which is updated to the latest firmware, before you ask). Here is the trap: I grab my smartphone, open the default camera app, zoom a bit and take a picture, like the one below.
Then I open up my image in Authenticate, go to the Thumbnail filter, and… oops!
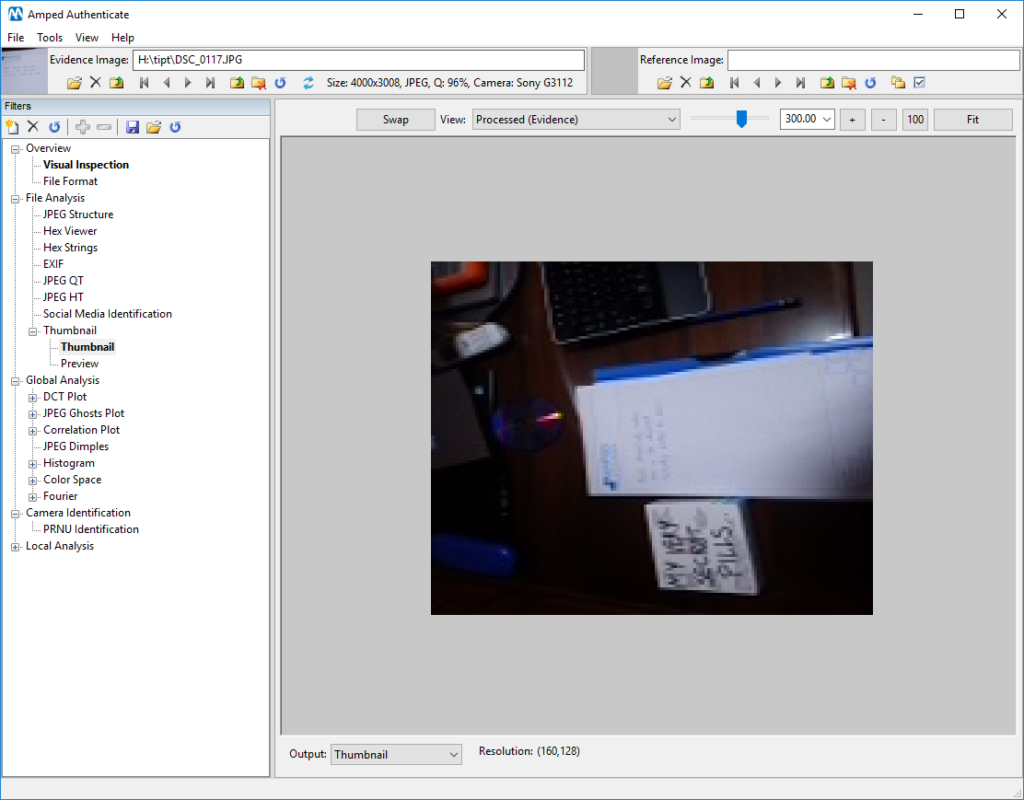
There’s quite a bit more here than in the full-size image! It turns out, my smartphone creates the thumbnail using my full sensor content, not just the zoomed area. I’ve found the same issue on other images on Flickr (e.g., this one), captured with the same model… so it’s not just my phone.
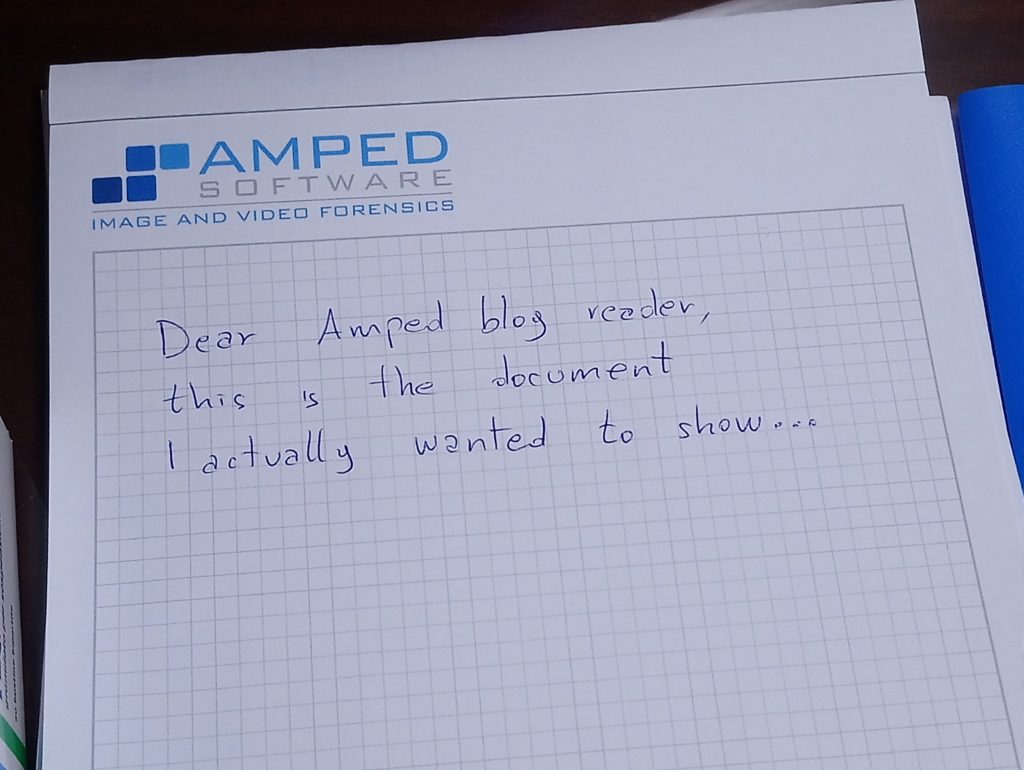
There’s a box on the left of the document, but the writing on it is a bit messy… since I’m an image & video forensics professional, I undoubtedly must have Amped FIVE in my toolset! It would be nice to enhance the thumbnail image a bit. How can I take it out?
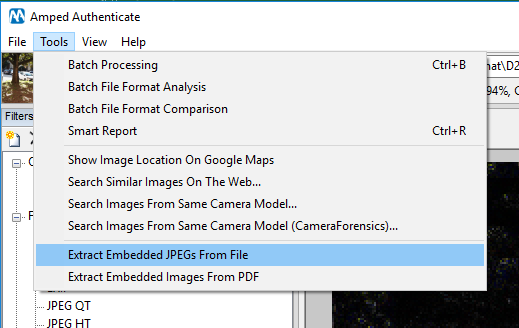
There’s a handy tool in Authenticate called Extract Embedded JPEGs From File: it extracts the embedded thumbnail, preview (and possibly other embedded JPEG images) to separate files in your computer. It’s just a bit of an unpacking process, no recompression occurs, so it’s the best option from a forensic perspective.
Great, now I grab the extracted thumbnail image in Amped FIVE, apply some filters, and… there we go!
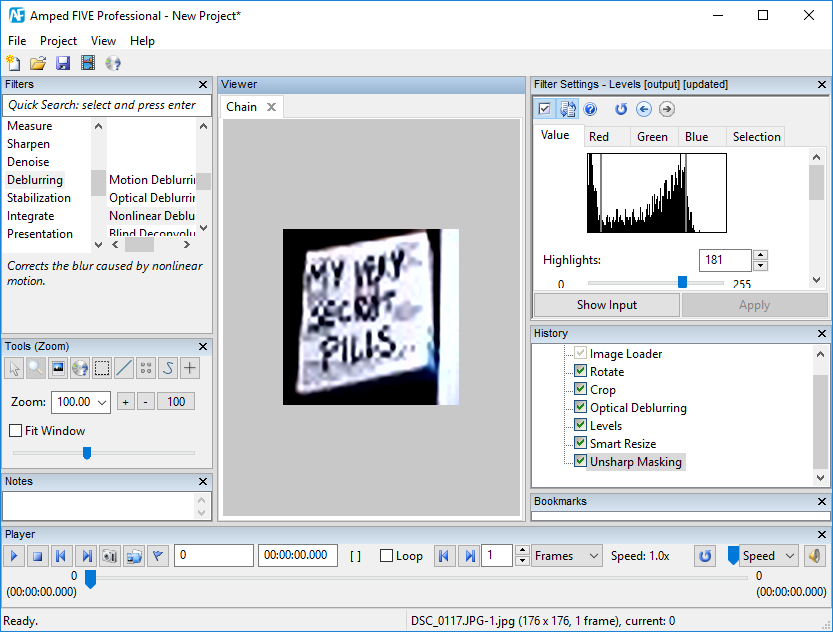
Aiming to share the picture of a handwritten document, I unintentionally revealed to the world that I make use of My very secret pills, whose box was sitting on my desk. Dangerous, isn’t it?
There’s much more you can do in Authenticate for analyzing the thumbnail and preview, for example, you can analyze their JPEG Quantization Tables, JPEG Huffman Tables, etc. But this will be the subject of a future Tip Tuesday!
This week’s takeaway is: better to take a look than to overlook! Even the simplest filter could prove crucial to your analysis.




