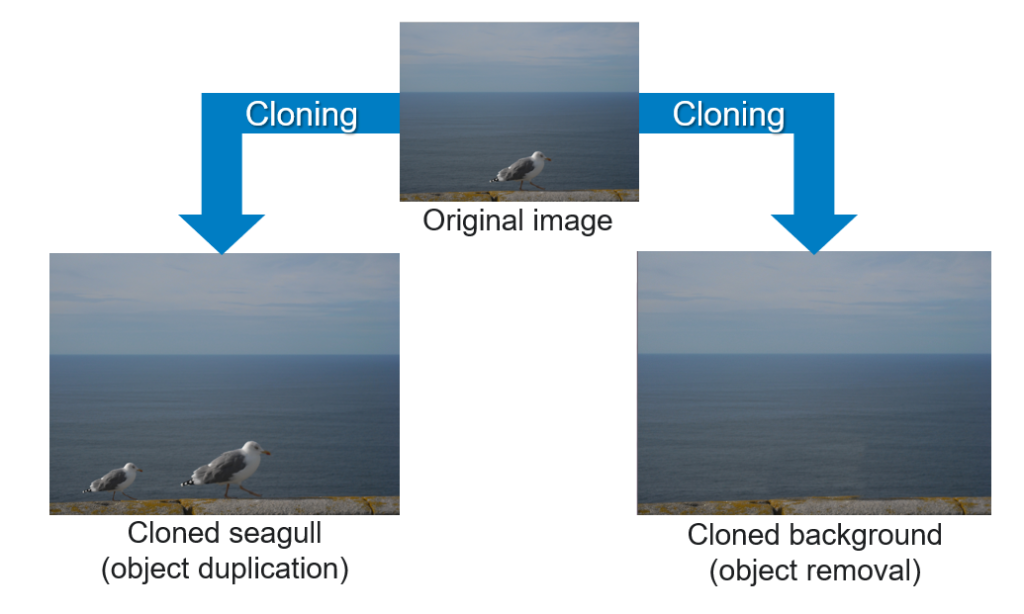
Clone detection (aka “copy-move detection”) is a very important image authentication task. Clones are a special case of image manipulation where part of an image is copied, possibly resized, rotated, sheared, etc., and then pasted to another region of the same image. The two main applications of cloning are:
- creating multiple (fake) copies of an object through copy-paste;
- removing an object from the scene by covering it with a cloned portion of the background.
This is explained with a very simple example in the image below.
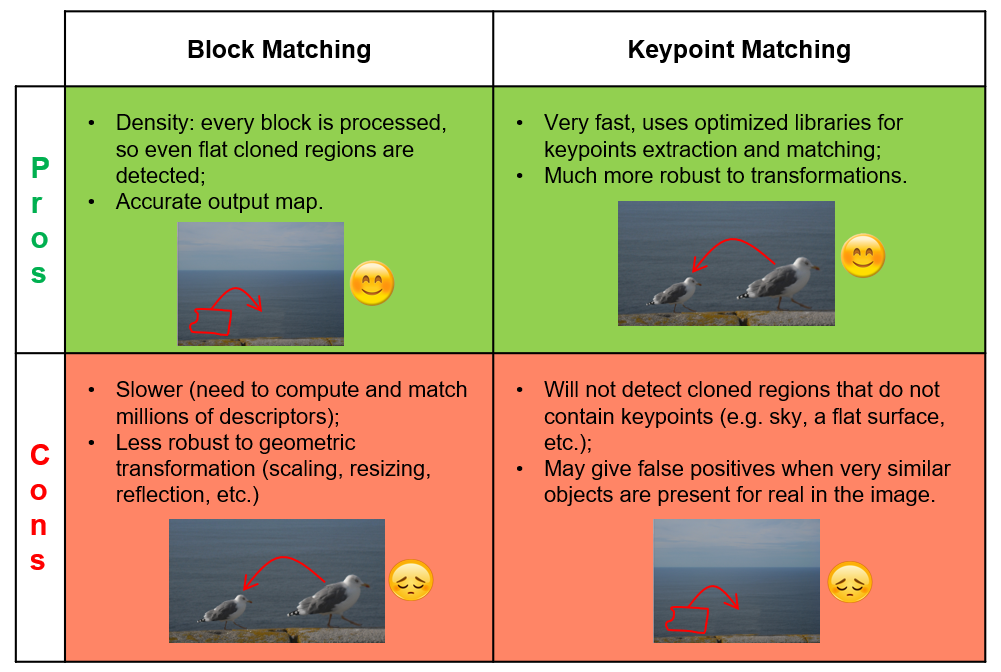
The image forensics research community worked hard to develop techniques for clone detection, and two main approaches have been invented: block-matching and keypoint-matching. As suggested by their names, they are based on two different strategies, briefly explained below.
Block-matching approach
- Split the image in overlapping blocks;
- Compute a digest (“descriptor”) for each block, possibly robust to rotation, scaling, compression, etc.;
- Search for clusters of matching descriptors.
Keypoint-matching approach
- Detect keypoints (SIFT, SURF, BRISK, etc.) from the image;
- Compute keypoint local descriptors;
- Search for (clusters of) matching keypoints.
Which one is better? It depends, and we try to explain why with the table below:
So, if your question was: “Do I need a block- or a
That’s why Amped Authenticate features both algorithms under the Local Analysis category: Clones Keypoints and Clones Blocks. Let’s compare their output on the sample image we used in this article:
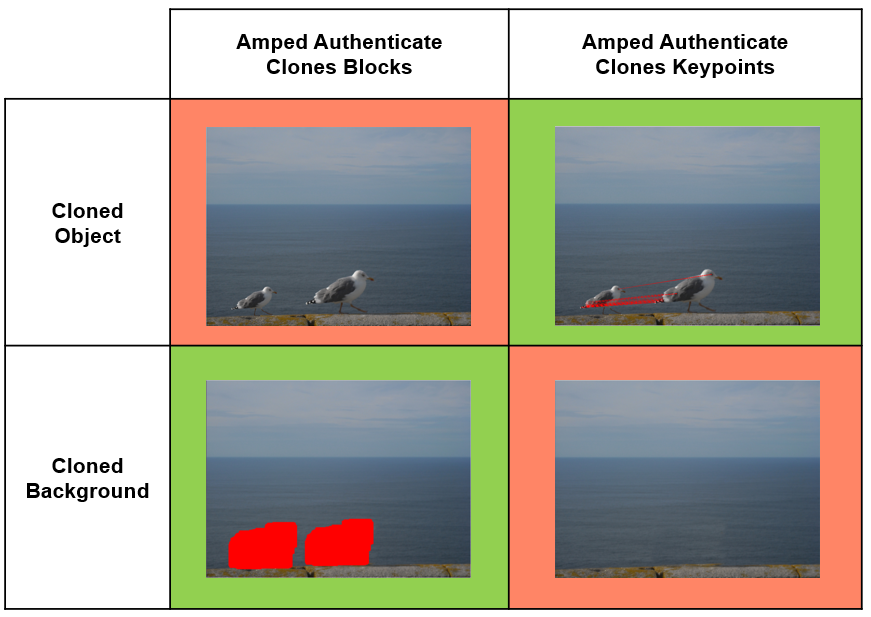
We see that the cloned seagull (top row) is detected by the Clones Keypoints despite the strong down-scaling applied to the cloned object; such a geometrical transformation is too strong to be detected by Clones Blocks. On the other hand, Clones Blocks successfully detects the cloned background (bottom row), that is not detected by Clones Keypoints because the cloned area is just too flat and it does not contain enough keypoints.
We hope you enjoyed this quick tip! Stay tuned and don’t miss our next #ampedtiptuesday post!




