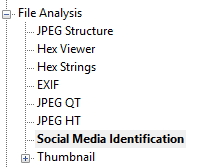
Amped Authenticate Update 10641 introduced the new Social Media Identification filter. It can be found in the File Analysis filter group.
The filters in the File Analysis group are generally looking at the file’s container to return relevant information about the file. The Social Media Identification filter examines the file for traces of information that may indicate the file’s social media source. The key word here is “may.”
The workflow that I will explain here is typical in the US and Canada. Take from it what you need in order to apply it to your country’s legal system.
Let’s begin.
Courts rely on authentic evidence. Evidence codes demand that the party submitting evidence declare the evidence to be contextually authentic – it is what it’s supposed to be and is relevant/ material in helping the Trier of Fact understand the facts of the case. As an example, the Canada Evidence Act (R.S.C., 1985, c. C-5) 31.1 notes, “Any person seeking to admit an electronic document as evidence has the burden of proving its authenticity by evidence capable of supporting a finding that the electronic document is that which it is purported to be. 2000, c. 5, s. 56.” In the US, if evidence is shown to be relevant, material, and competent, and is not barred by an exclusionary rule, it is admissible (Fed. Rules Evid. 402).
Image-based evidence is either “Real” or “Demonstrative”. Real Evidence is a thing the existence or characteristics of which are relevant and material. Real Evidence can be authenticated by the person who created the evidence, a person depicted in the evidence, or a third party scientific authenticator (like you or I using Amped Authenticate). Demonstrative Evidence is just what the name implies, it demonstrates or illustrates the testimony of a witness. It will be admissible when, with accuracy sufficient for the task at hand, it fairly and accurately reflects that testimony and is otherwise unobjectionable.
To understand Real Evidence, let’s say I take a selfie (picture) with my iPhone. I then upload that picture to my Facebook account. I later download that picture from Facebook to my computer. The downloaded photo isn’t a camera original. Facebook will have resized and recompressed it. My computer may add information to the container as well. Database type authentication tools will reject this file, declaring it not authentic because the EXIF data and other elements of the camera are stripped out by Facebook. But, I took the photo. It’s a photo of me. I can authenticate it as both the photographer and the subject. If I took a photo of a traffic collision scene, and it followed the same path, it may be considered Demonstrative Evidence as it will likely be used to demonstrate the elements of the collision.
But what happens when an investigator downloads a file from social media and doesn’t have the supporting testimony of the photographer or the subjects in the scene? That’s where we as analysts come in.
In People v. Beckley (2010) 185 Cal.App.4th 509, the trial court admitted a photograph downloaded from the MySpace Web page of one of the defendants. (Beckley, supra, 185 Cal.App.4th at p. 514.) The photograph purportedly depicted the defendant’s girlfriend making a gang sign, and was introduced to rebut her testimony that she was not associated with a gang. (Ibid.)
The appellate court held that the trial court erred in admitting the photograph because there was not any “evidence sufficient to sustain a finding that it is the photograph that the prosecution claims it is, namely, an accurate depiction of the girlfriend actually flashing a gang sign.” (Id. at p. 515.) The detective could not testify from personal knowledge that the photograph truly portrayed the girlfriend flashing a gang sign, and no expert testified that the picture was not a composite or faked photograph. (Ibid.)
Thanks to case law like Beckley (2010), investigators and attorneys will need to test the authenticity of social media images before submitting them to the case.
As with Beckley (2010), a challenge to the authenticity of an image/video should be specific and testable. The challenge in Beckley (2010) was that of cut/paste forgery – someone had “Photoshopped” the image to change important contextual information. It didn’t matter who may have “Photoshopped” the image, only that the prosecutors hadn’t authenticated the image nor could they effectively respond to the challenge.
Fast forward to today. Investigators and attorneys have the ability to conduct authentication examinations prior to submitting evidence into a proceeding. With Amped Authenticate, they have the power of over three dozen tests that can look not only at a file’s integrity but also its contextual authenticity.
The new Social Media Identification filter is an important piece of the puzzle, but interpreting the results requires training. Images floating around social media are often shared between platforms. You’ll see something cool on Instagram and share it on your Facebook page. You’ll post something on LinkedIn, which can simultaneously post it to your Twitter feed. Someone may like it, and send it to their Tumblr or Flickr account. Depending on how this activity happens, the file’s attributes may change and/or the file may be recompressed. Understanding how all of this works is the value of training.
There are then two general types of authentication examinations, blind and specific. The blind test is the kind done ahead of submission to assure that an image hasn’t been “Photoshopped.” Depending on the source, these tests may be inconclusive. These are also the hardest tests to complete and to support your findings. Specific tests are the result of a specific and testable allegation of forgery – someone “Photoshopped” me into a scene, someone cropped the image to remove the real culprit, etc.
Let’s say you want to use an image found on the defendant’s mobile phone. You’ve used a lot of the various available mobile phone forensics tools which will hash the results of the acquisition. But a hash value isn’t proof of authenticity, it’s an integrity check to assure the integrity of the file through the process. It can’t help you if the file was “Photoshopped” before it arrived on the phone.
This is the value of Amped Authenticate – testing contextual authenticity. It can work synergistically with other tools and within other disciplines. Mobile Device Examiners, Computer Forensic Examiners, and Forensic Multimedia Analysts now have a tool available to test the contextual authenticity of the files they’re working with. You certainly don’t have to test every file that was found in the device, but you should test those files that will be submitted as evidence. Remember, Authenticate’s Batch Processing function can speed up the process of authenticating large volumes of files.
Using social media files in investigations is fraught with complexity. They’re not camera originals. You likely can’t authenticate based on the photographer/subject. You’ll need a tool to help answer questions about the file ahead of trial and respond to any challenges raised. With Amped Authenticate, you have it. With our latest update and the new Social Media Identification filter, you have the ability to examine the file’s context and provenance a bit closer.
For more information on our products and training, click here to contact us today.