
We’ve just launched some pretty important additions to Amped Authenticate. Not only have we integrated it with CameraForensics, but we have also made some major improvements to the quantization tables in addition to many other internal improvements. Read below for the details.
CameraForensics Integration
The main purpose of Amped Authenticate is to verify if a picture is an original coming from a specific device or if it’s the result of manipulation using image editing software. One of the main tests to verify the file integrity is to acquire the camera that is assumed to be the one that has generated the photo (or at least the same model) and verify if the format is compatible with the file under analysis.
While this sounds easy in practice, many devices have so many different settings and because of this it can be challenging to recreate the same conditions. Furthermore, the camera is often not available.
What if we look on the web for pictures coming from a specific device? While we cannot, in general, guarantee the integrity of files downloaded from the web, we can triage them pretty easily and do a comparison with the image under analysis.
But how do you search for images on the web in an efficient manner? We have had “Search for Images from Same Camera Model…” in Authenticate for quite some time. It allows you to search on Google Images and Flickr, but the search is not always optimal, as it has to apply different workarounds to work efficiently in a forensic setting.
So, what if someone built a database of pictures on the web, optimized for investigative use, enabling you to instantly search for images coming from a specific device and with specific features such as resolution and JPEG quantization tables? Turns out the guys at CameraForensics did exactly this (and much more) and we partnered with them to provide a streamlined experience.
Let’s see how it works.
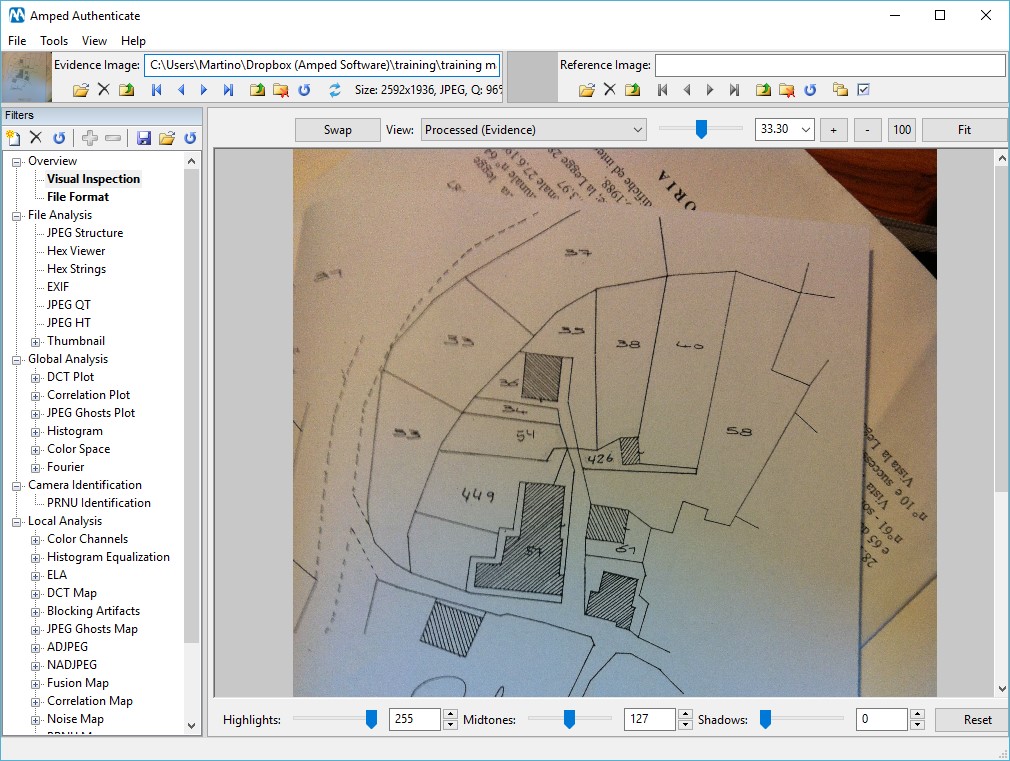
So, say we are analyzing a photo of a document, that we suspect may be modified.
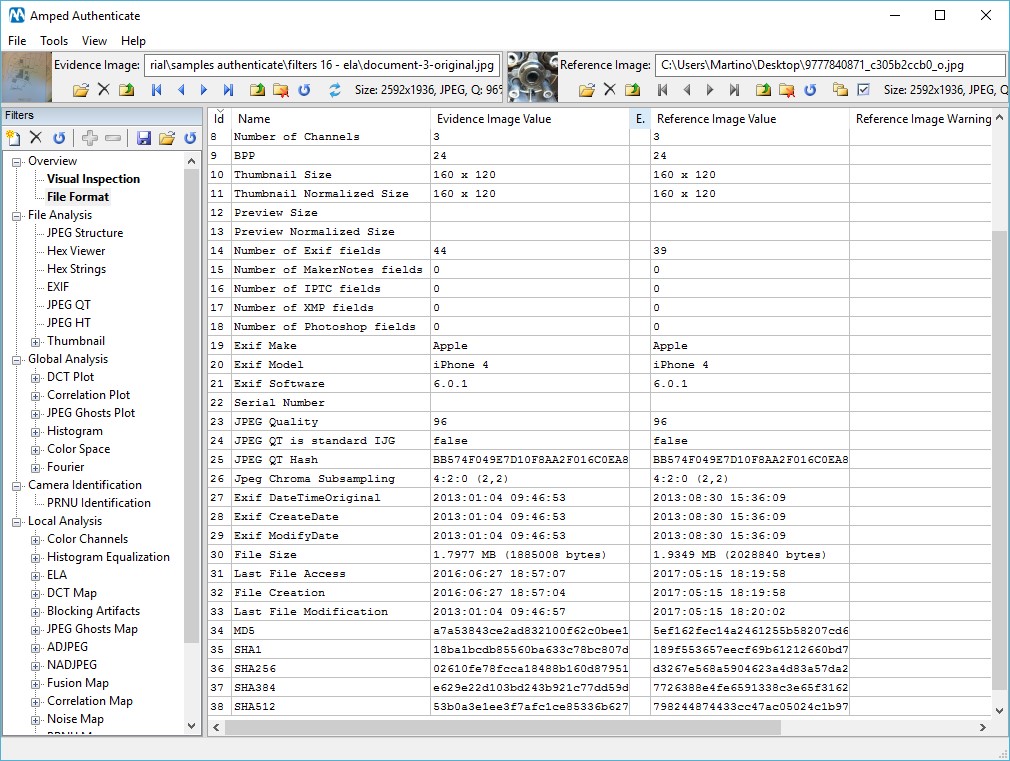
By analyzing the metadata, we see that the image is coming from an Apple iPhone 4.
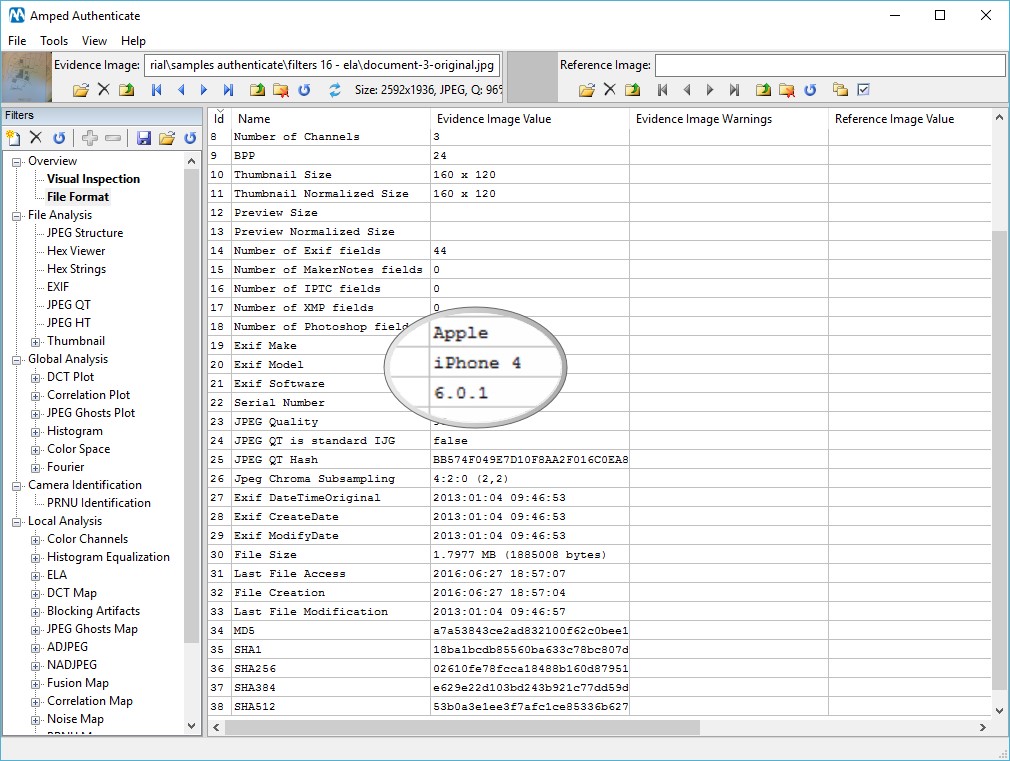
The question we then need to ask: is the format consistent with what we should expect from an iPhone 4? This includes the file format, JPEG structure, EXIF and other metadata and JPEG features such as quantization tables and Huffman tables. We don’t have an iPhone 4 handy, but we can search for pictures coming from this device thanks to the CameraForensics integration.
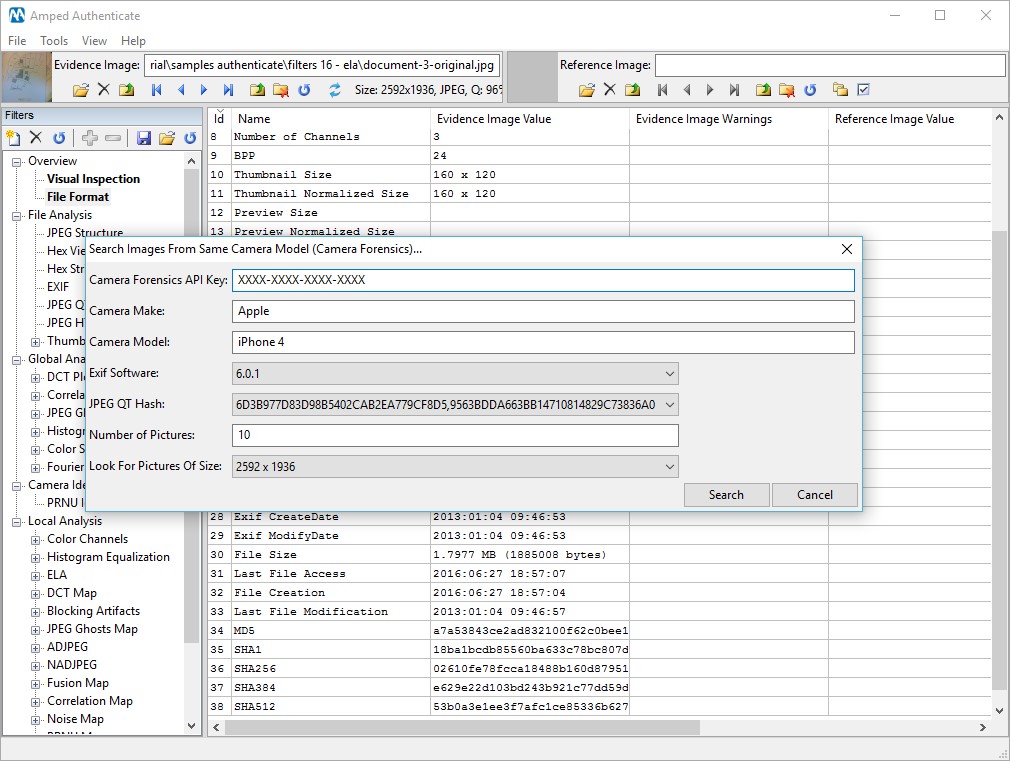
As you can see in the screenshot below, Amped Authenticate automatically populates the fields: Camera Make, Camera Mode, EXIF Software, JPEG QT Hash and Picture Size. The user, however, can change any of these to have a less restrictive search. By default, the software provides the first 10 results, but we can have many more.
The search function immediately provides you with a list of images that can be selected and downloaded to the workstation.
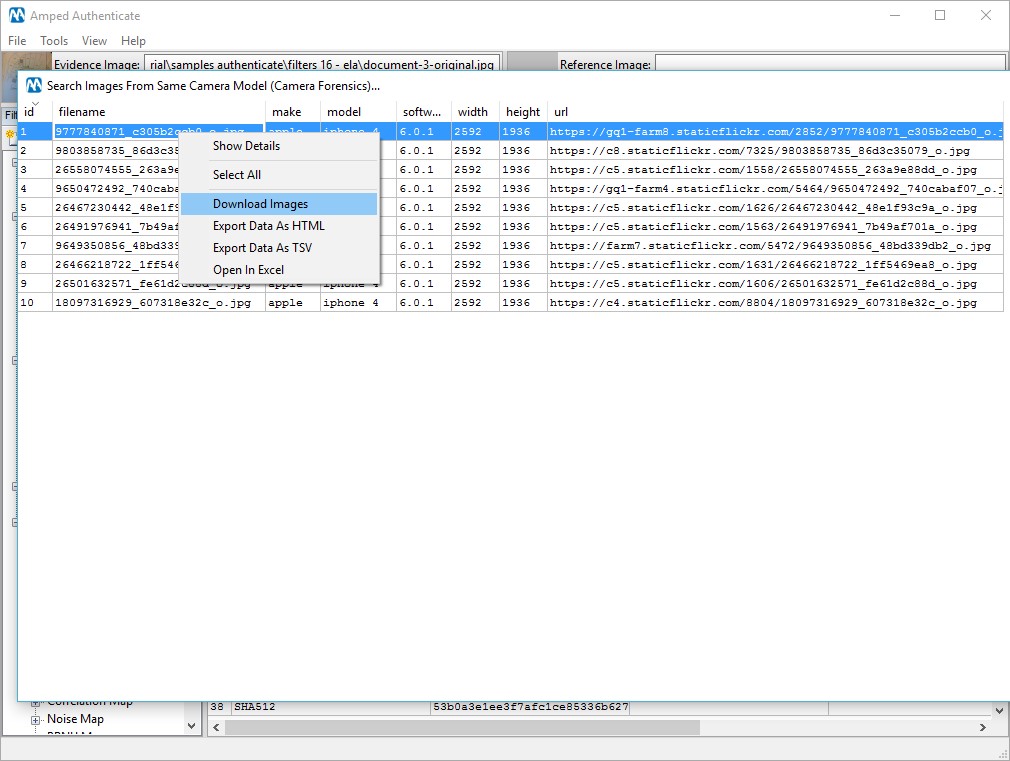
Once downloaded, the pictures can be compared with the image under analysis. We don’t care about the content of the picture but only about the format. In this case, it looks like we found some pictures from an iPhone 4 that are fully compatible with our evidence.
It should be noted that in terms of image authentication, it is very difficult, if not impossible, to be sure about what’s real and what’s not, and even more so when analyzing images from the web. Additionally, a very experienced attacker could simulate the format of a picture coming from a specific device, but it would be very difficult to pass all the tests.
In order exploit the power of the CameraForensics integration you need to have an active account with them, you can find more information on http://www.cameraforensics.com/amped.
New QT Database
Another feature in Amped Authenticate that helps you verify the image integrity and its source, is the newly expanded and improved quantization tables database. What is this? In laymen terms, quantization tables (QTs) represent the JPEG compression settings of a picture. Different camera models and software tend to use different QTs. So what we created is a database of known QTs for different sources.
We did a very comprehensive study, lasting several months, targeted at finding general differences between camera original images and images processed with some image editing software. The new QT database is just one of the many results we have obtained.
Just to give you some numbers:
● We analyzed 46,834 images acquired from various sources. Unless testing explicitly from a software source, we tried to acquire only images which we expected to be camera original.
● The images were coming from 1,394 different devices from 83 different brands.
● We found 19,708 different unique compression signatures (including other metadata in addition to the QTs).
● We found 1,717 unique QTs for the luminance.
If you now go to JPEG QT in Amped Authenticate and click on the button “View All QTs In Database” you will get this dialog.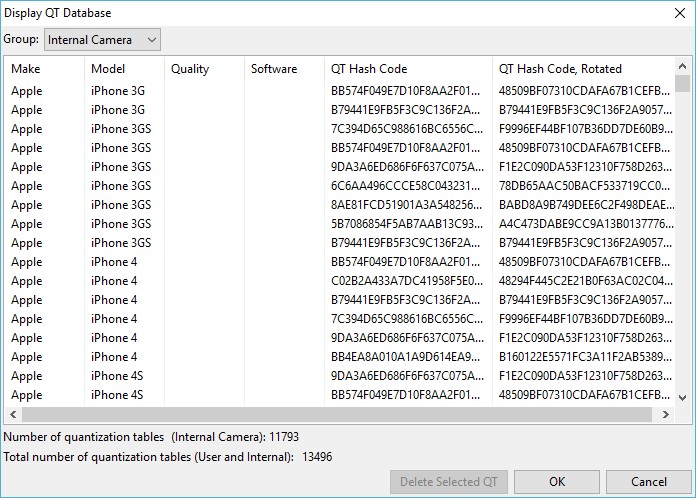
As you can see the current version has almost 13500 Make/Model/QT combinations.
Of course, given how QTs are calculated in some camera models and the continuous release of new models of cameras and smartphones, the database will never be exhaustive, but you can still search the web for compatible QTs thanks to the CameraForensics integration that was mentioned above.
That’s not all, folks…
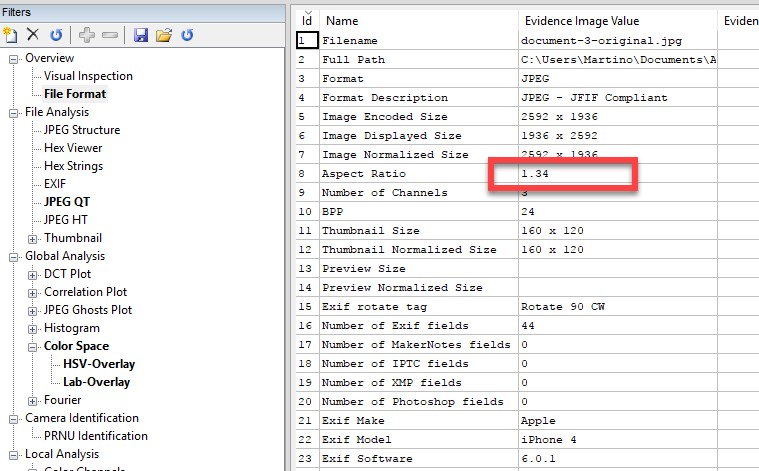
File Format: added the filed aspect ratio and removed the misleading field “Orientation”.
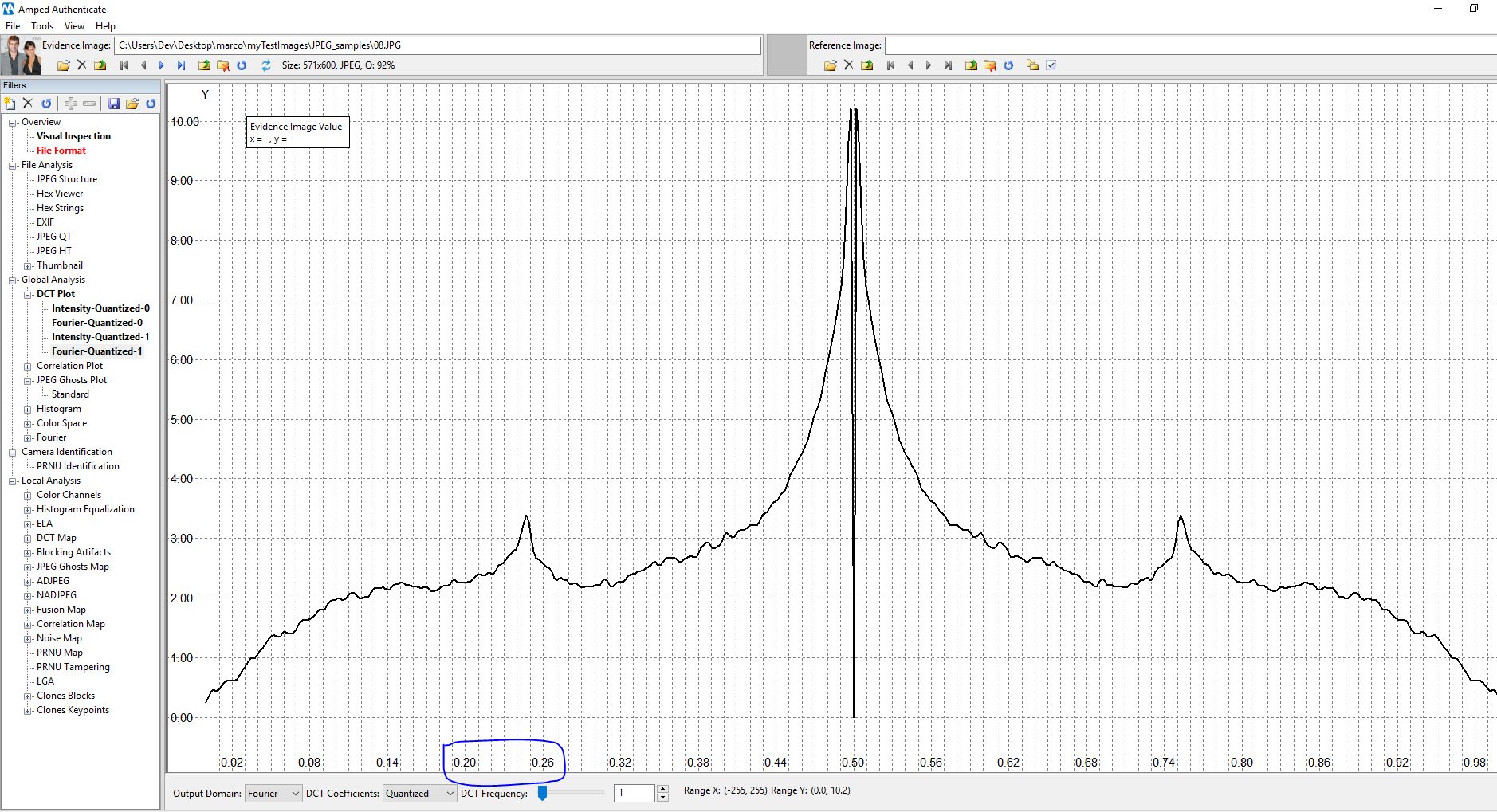
DCT Plot: we changed the x-axis labels to normalized frequencies in order to facilitate the understanding of the period of possible periodic patterns.
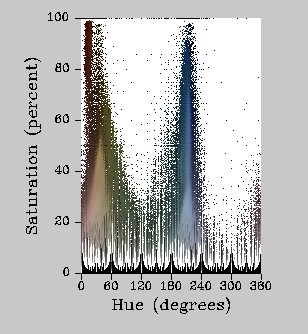
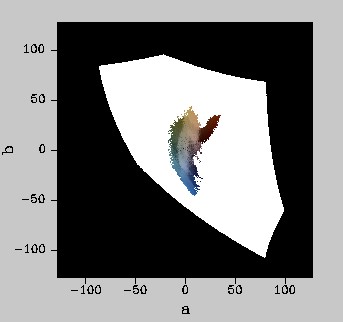
Color Space: we added legends to have better quantitative information.
PRNU Identification and PRNU Tampering: now the camera reference pattern file (CPR) is synchronized between the two filters. Further algorithm improvements have also been made.
DCT Map: photos with EXIF rotate tags set were displayed in the wrong orientation. This has now been fixed.
Clones Blocks: the mask was inverted when reloading the results multiple times from the cache. This has now been fixed.
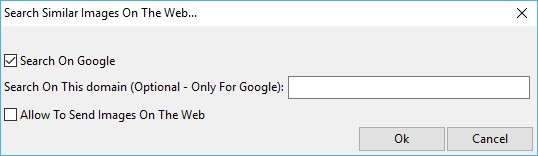
Search Similar Images On The Web: unfortunately, TinEye keeps changing the API so we had to disable it, so for the moment we support only Google Images. We plan to put it back in the next version.
And many more improvements under the hood…
Renew now!
That’s it for now. For Amped Authenticate users with up to date support, please remember to “Check for Updates Online” to download this update or contact us to renew your SMS plan.




