A key amendment to US Federal Rules of Evidence 902, in the form of new subsection (14), will go into effect on December 1, 2017. The committee note on the proposed rule lists the following as the justification for the addition of subsection 14:
“The amendment sets forth a procedure by which parties can authenticate data copied from an electronic device, storage medium, or an electronic file, other than through the testimony of a foundation witness. As with the provisions on business records in Rules 902(11) and (12), the Committee has found that the expense and inconvenience of producing an authenticating witness for this evidence is often unnecessary. It is often the case that a party goes to the expense of producing an authentication witness, and then the adversary either stipulates authenticity before the witness is called or fails to challenge the authentication testimony once it is presented. The amendment provides a procedure in which the parties can determine in advance of trial whether a real challenge to authenticity will be made, and can then plan accordingly.
Today, data copied from electronic devices, storage media, and electronic files are ordinarily authenticated by “hash value.” A hash value is a unique alpha-numeric sequence of approximately 30 characters that an algorithm determines based upon the digital contents of a drive, media, or file. Thus, identical hash values for the original and copy reliably attest to the fact that they are exact duplicates. This amendment allows self-authentication by a certification of a qualified person that she checked the hash value of the proffered item and that it was identical to the original. The rule is flexible enough to allow certifications through processes other than comparison of hash value, including by other reliable means of identification provided by future technology.“
Whilst the commentary from the committee doesn’t specifically list the reasons behind the addition, other than limiting the expense of having someone testify unnecessarily, the roots of this change can be found in the SCOTUS case Melendez-Diaz vs. Mass. This case reaffirmed the 6th Amendment rights of the accused to confront his/her accusers. The impact of this case meant that everyone who did anything for a case was often subpoenaed to be in court. Things that could easily be stipulated to and weren’t in question – like testifying about the authenticity of a digital file that had a clean chain of custody and a verifiable hash value – were now tying up staff (as they waited in courtroom hallways to testify) and driving up costs. Again, the commentary on the rule doesn’t mention this case, but impacted labs can see the connection quickly.
Assuming that the employees involved follow SOPs and best practices, files downloaded from digital devices and hashed are what’s dealt with in this rule. Computer forensics and eDiscovery folks are already cheering this change. But it’s obvious that it will impact our domain as well. After all, what is DME but digital files downloaded from a digital storage device.
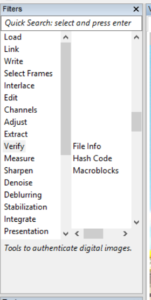
Where we have you covered is in hash value calculation and reporting. In Amped FIVE, you have the ability to calculate the hash value of the loaded file. You’ve had this ability for quite some time, I might add. How to do it:
- Load the file. (Load>Image Loaded / Video Loader)
- Calculate the hash. (Verify>Hash Code)
- Insert the file’s EXIF data into the report (Verify>File Info)
- Then, work the workflow to answer the question … The workflow will be self-evident as the reader moves down the report (restoration / clarification / analysis / presentation)
As you already know, Amped Software reports are second to none – clearly detailing the steps performed in your analysis.
Of course, the FRE deals with US Federal Courts. But, most US state evidence codes mirror the FRE. It’s likely that this change will filter down to state courts over the next few years – especially in those states facing budget problems.
For more information about how our leading-edge tools can help your lab, click here.